This article is sponsored by Intuit.
When a company has a dozen employees, managing access to financial systems is straightforward. The owner, an accountant and maybe a bookkeeper can share a single accounting platform without much concern about who sees what. But as organizations scale past 100 employees and begin operating across multiple departments, locations or subsidiary entities, the question of data access becomes far more consequential.
Consider the risks: your sales team probably shouldn’t have visibility into payroll data. A subsidiary’s financial statements may need to remain isolated from other business units. External accountants and auditors need enough access to do their work, but not a byte more. Without the right controls in place, sensitive information leaks across organizational boundaries, creating compliance liabilities, competitive risks and a fertile environment for fraud.
This guide walks through how growing organizations can implement role-based access control (RBAC) and data segregation strategies within their ERP systems to protect sensitive financial information while still enabling the collaboration their teams need to operate effectively.
Why data segregation matters for growing businesses
Data segregation is the practice of restricting access to information based on organizational role, department or entity. It’s an IT best practice and a business requirement that touches security, compliance and operational efficiency.
- Security risks are the most immediate concern. According to the Verizon 2025 Data Breach Investigations Report, roughly 60% of data breaches involve human activity – including that by internal actors – whether through malicious intent, negligence or compromised credentials. The Ponemon Institute’s 2025 Cost of Insider Risks report puts the average annual cost of insider-related incidents at $17.4 million per organization. These aren’t just statistics that affect Fortune 500 companies, either; mid-sized businesses with loose access controls face the same categories of risk, often with fewer resources to recover.
- Beyond security, there are operational reasons to segregate data. Department managers should be able to run their operations without accidentally modifying another team’s records. Subsidiaries often need financial independence from a parent company. And external collaborators, like accountants, auditors and consultants, need carefully scoped access that expires when their engagement ends.
- Regulatory compliance adds another layer of urgency. Depending on your industry, frameworks like the Sarbanes-Oxley Act (SOX), the General Data Protection Regulation (GDPR), or industry-specific standards such as HIPAA or PCI-DSS may require documented access controls and audit trails. Failed compliance audits can result in penalties, legal liability and reputational damage.
The Verizon 2025 DBIR found that roughly 60% of data breaches involve the human element, including from internal actors. Proper user permissions and role-based access controls are your first line of defense against both malicious and accidental insider exposure.
Understanding role-based access control
What Is RBAC?
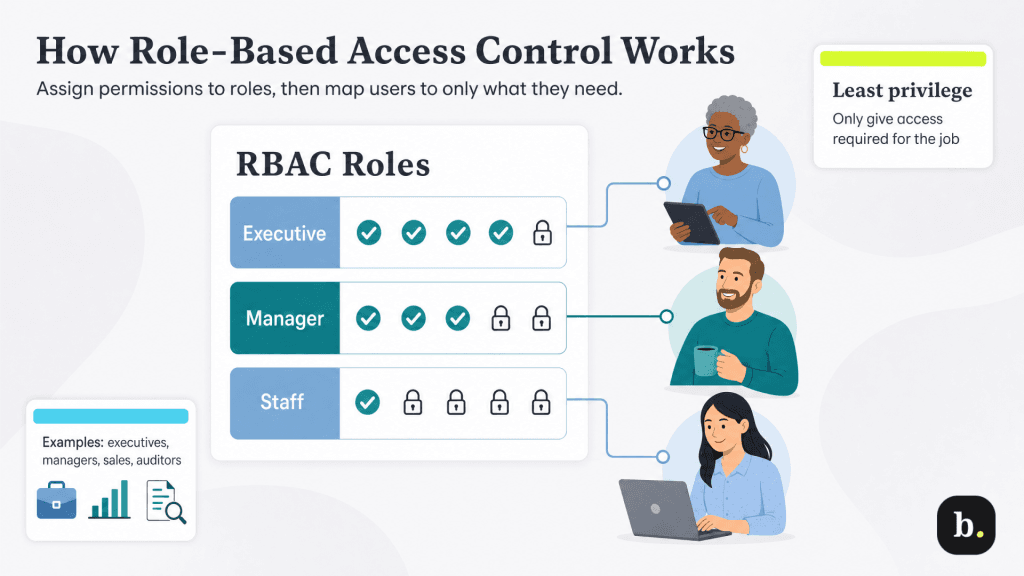
Role-based access control is a permissions model that assigns system access based on a user’s job function rather than granting permissions to individuals on a case-by-case basis. Instead of deciding that Jane in accounting can view invoices and Bob in sales can see customer records, you define roles like “Accounting Manager” or “Sales Representative”. You would then attach a certain set of permissions to those roles; when users are assigned to the appropriate role, they would inherit its permissions automatically.
The underlying principle is called “least privilege”: every user gets the minimum level of access required to perform their job, and nothing more. This differs sharply from the all-or-nothing approach that many small businesses fall into, where employees either have full system access or are locked out entirely.
Common role structures
While every organization’s role hierarchy will look a little different, most mid-sized businesses share a common pattern:
- Executive leadership: Full visibility across all entities, including consolidated reporting and financial planning.
- Department managers: Access restricted to their own department’s transactions, budgets and reports.
- Accountants and bookkeepers: Financial data access for transactions, reconciliation, and reporting—but no visibility into HR or payroll records.
- Sales teams: Customer records, invoices and pipeline data, but not cost-of-goods, vendor terms or financial statements.
- External auditors: Read-only, time-limited access scoped to the specific records and periods under review.
Leading ERP platforms like Intuit Enterprise Suite come with predefined roles, including company administrator, bookkeeper, project manager and payroll manager. They also allow administrators to create custom roles with specific permissions tied to features and transaction types. Roles and permissions can be managed across multiple entities from a single login, which is particularly valuable for organizations with complex structures.
Permission levels
Within each role, permissions typically operate across several dimensions. At the most basic level, users may be granted the ability to view, create, edit, delete or approve records. But effective RBAC goes deeper: you’ll want to distinguish between report access and transaction access (a user might need to view financial summaries without being able to modify individual journal entries,) and you’ll need data export controls to prevent unauthorized bulk downloads of sensitive records.
For example, a department manager might have full create-and-edit access to expense reports within their department, view-only access to company-wide budget summaries and no access to payroll records or bank account details. Mapping out a permission matrix like this before configuring your system prevents the common pitfall of granting overly broad access during initial setup and trying to rein it in later.
Multi-entity and subsidiary segregation
Why separate entities need isolated data
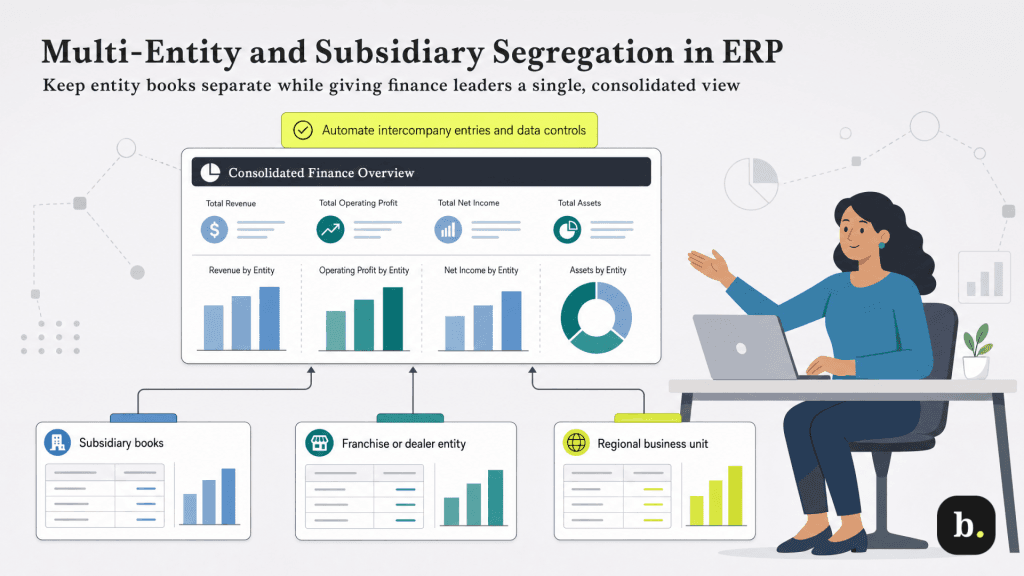
When a business operates through multiple legal entities such as subsidiaries, holding companies, franchises or geographically distinct operations, each entity often has legal, competitive or operational reasons to maintain financial independence. A subsidiary may be required by law to maintain its own books. Franchise or dealer networks may include competitors who should never see each other’s financial performance. And business units operating in different regulatory environments may need to comply with different data-handling requirements.
At the same time, leadership needs consolidated visibility. The CFO needs to see how the whole portfolio is performing; the board needs consolidated financial statements; and the parent company needs to manage intercompany transactions and elimination entries for accurate reporting. The challenge is delivering both operational isolation at the entity level and consolidated intelligence at the top.
How ERP systems handle multi-entity architecture
Modern ERP platforms address multi-entity management through a shared-infrastructure model. Each entity maintains its own general ledger and transactional data, but all entities live within a unified platform that enables cross-entity reporting and management from a single interface.
Intuit Enterprise Suite takes this approach natively. Administrators can manage all entities from one account with a dropdown entity switcher, support up to 500 users with customized access permissions and run consolidated financial statements across the entire portfolio. The platform handles intercompany transactions automatically as well; when one entity invoices another, matching receivable and payable entries are created without manual journal entries, and elimination entries for consolidated reporting are generated automatically. This is a meaningful departure from legacy approaches, such as maintaining separate QuickBooks subscriptions for each entity and manually reconciling intercompany transactions at month-end.
Intercompany transactions
Intercompany billing is one of the most sensitive areas in multi-entity accounting, and it’s also where poor access controls cause the most confusion. When Entity A charges Entity B for shared services, the system needs to create matching entries on both sides of the ledger, maintain a clear audit trail, and ensure that users at Entity B can see the invoice without gaining access to Entity A’s broader financial data.
A properly configured ERP will automate these transactions through predefined intercompany account mappings, generate the elimination entries needed for consolidated reports and restrict cross-entity visibility so that operational users only see their own entity’s data. Finance leaders can then view the full picture through consolidated dashboards without compromising entity-level isolation.
Plan your entity structure and role hierarchy before implementation. Retrofitting data segregation after users already have broad access creates both political and technical challenges—it’s much harder to take access away than to grant it thoughtfully from the start.
Technical security features in modern ERPs
Authentication and access controls
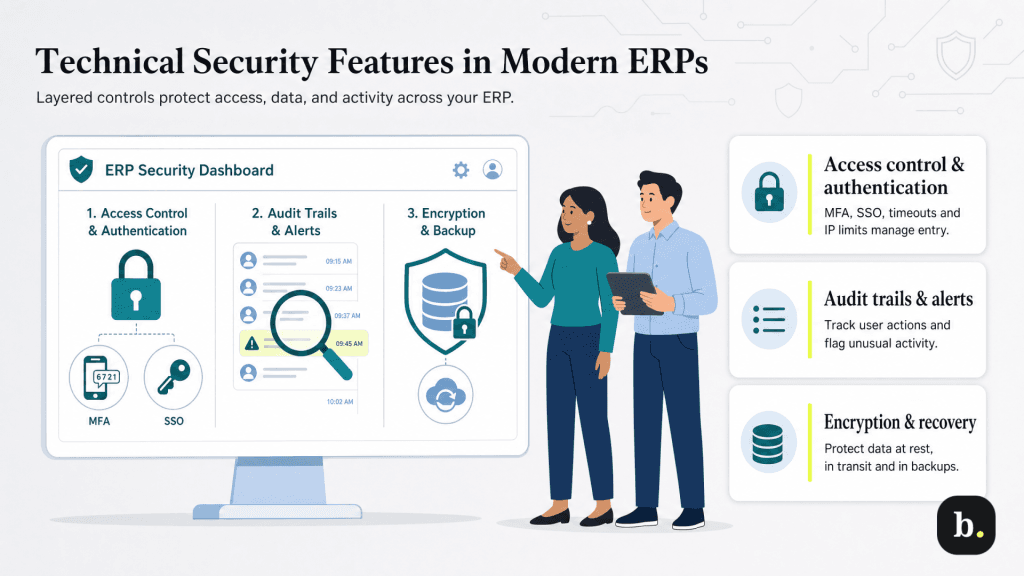
RBAC defines what users can do once they’re inside the system. Authentication controls determine who gets in at all. For growing organizations, several layers of authentication security should be non-negotiable:
- Multi-factor authentication (MFA): Requires users to verify their identity through a second method – typically an authenticator app or SMS code – in addition to their password. Intuit’s platform supports MFA natively, and security best practice recommends making it mandatory for all users rather than optional.
- Single sign-on (SSO) integration: Allows employees to use their corporate credentials (such as those managed through Azure Active Directory, Okta, or Google Workspace) to access the ERP, reducing password fatigue and centralized credential management.
- Session timeout policies: Automatically log out inactive users to prevent unauthorized access from unattended workstations, which is particularly important for shared office environments.
- IP address restrictions: For organizations with sensitive financial data, restricting ERP access to specific IP ranges adds a layer of protection against unauthorized remote access.
Audit trails and activity logging
Comprehensive audit trails are essential both for compliance and for detecting unusual behavior before it becomes a breach. An effective audit system tracks who accessed what data and when, maintains change logs for sensitive transactions (particularly journal entries, payment approvals and account modifications), and generates alerts for unusual access patterns, such as a user suddenly downloading large volumes of data or accessing records outside their normal scope.
These logs also serve a practical purpose during external audits. When an auditor asks to verify who approved a specific transaction or when a particular account was modified, a detailed audit trail provides the answer instantly.
Data encryption
Data encryption protects information both at rest (stored on servers) and in transit (moving between user devices and the platform). Cloud-based ERP systems like Intuit Enterprise Suite use bank-grade 256-bit encryption, the same standard used by major financial institutions.
For especially sensitive fields like Social Security numbers, bank account details and routing numbers, field-level encryption adds an additional layer of protection. Field-level encryption ensures that even users with broad system access cannot view these specific data points unless explicitly authorized. Backup security and disaster recovery protocols should also be evaluated during ERP selection to ensure that your data remains protected and recoverable even in the event of a system failure or security incident.
Best practices for implementation
Implementing data segregation effectively requires as much organizational planning as it does technical configuration. These best practices can help ensure a smooth rollout:
- Conduct an access review during ERP selection: Before choosing a platform, map out your organization’s current and anticipated access requirements. This ensures the system you select can support the role structures you need.
- Document role definitions before configuration: Write out each role’s responsibilities and the specific permissions they require. This document becomes your configuration blueprint and your reference for future access reviews.
- Perform regular access audits: Quarterly reviews of who has access to what help catch permissions drift, the gradual accumulation of unnecessary access that occurs as employees change roles or take on new responsibilities.
- Build onboarding and offboarding checklists: Every new hire should receive access tailored to their role on day one. Every departing employee should have their access revoked immediately upon separation. Automate these processes wherever possible.
- Train managers on access request procedures: Department managers should understand how to request access changes through proper channels rather than sharing credentials or asking IT to “just give them the same access as Sarah.”
- Test segregation before go-live: Before launching a new ERP or migrating to a new permissions structure, test your role configurations thoroughly. Have users from each role verify that they can access what they need and nothing they shouldn’t.
Common pitfalls to avoid
Even organizations that invest in RBAC and data segregation can undermine their own efforts through a few common mistakes.
- Granting excessive permissions “just in case”: This is the most widespread issue. When a new employee joins and their manager isn’t sure exactly what access they’ll need, the path of least resistance is to grant broad permissions with the intention of scaling back later. In practice, that scaling-back rarely happens. Start with the minimum and expand as specific needs arise.
- Shared login credentials: These are another frequent problem, particularly in smaller teams or when onboarding is rushed. When multiple people use the same login, audit trails become meaningless—you can’t determine who actually performed a transaction—and you lose the ability to revoke one person’s access without affecting others.
- Failing to update access when employees change roles: This is a quieter but equally dangerous problem. An employee who moves from accounting to sales may retain their financial data access indefinitely unless someone actively reviews and adjusts their permissions. This is exactly the kind of permissions drift that regular access audits are designed to catch.
In general, beware of overly complex permission structures that frustrate users to the point of workaround behavior. If accessing a needed report requires three levels of approval, people will find shortcuts like emailing spreadsheets, screenshotting dashboards or simply asking a colleague with broader access to pull the data. The most secure system is one that makes the right behavior the easy behavior.