The right employee monitoring software can help you increase company security and employee productivity, but that doesn’t mean it’s easy to find. If you aren’t sure where to start, we’ve got you covered. We spoke with business leaders to hear firsthand on what to consider when choosing employee monitoring software – in addition to general monitoring features, of course.
Consider depth of monitoring features.
_*]:min-w-0 gap-3″>
The spectrum of monitoring capability across employee monitoring platforms is wide, and choosing the right depth depends heavily on what your organization actually needs to see.
On the lighter end, tools like Hubstaff and Time Doctor focus primarily on time tracking, activity levels, and basic app or URL usage, which is enough to confirm that hours are being logged productively without drilling into granular behavioral data. These are often sufficient for remote teams where the primary concern is accountability rather than security or compliance, and they tend to generate less friction with employees who may bristle at the feeling of being watched too closely.
_*]:min-w-0 gap-3″>
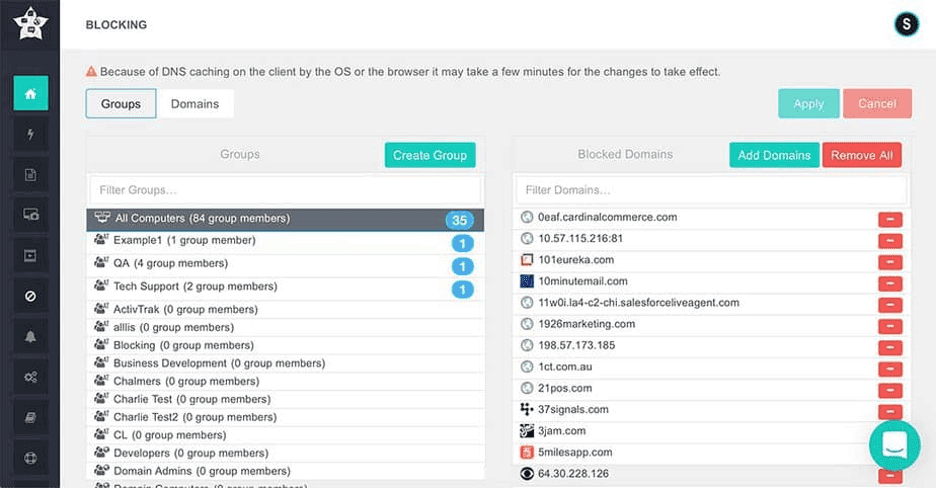
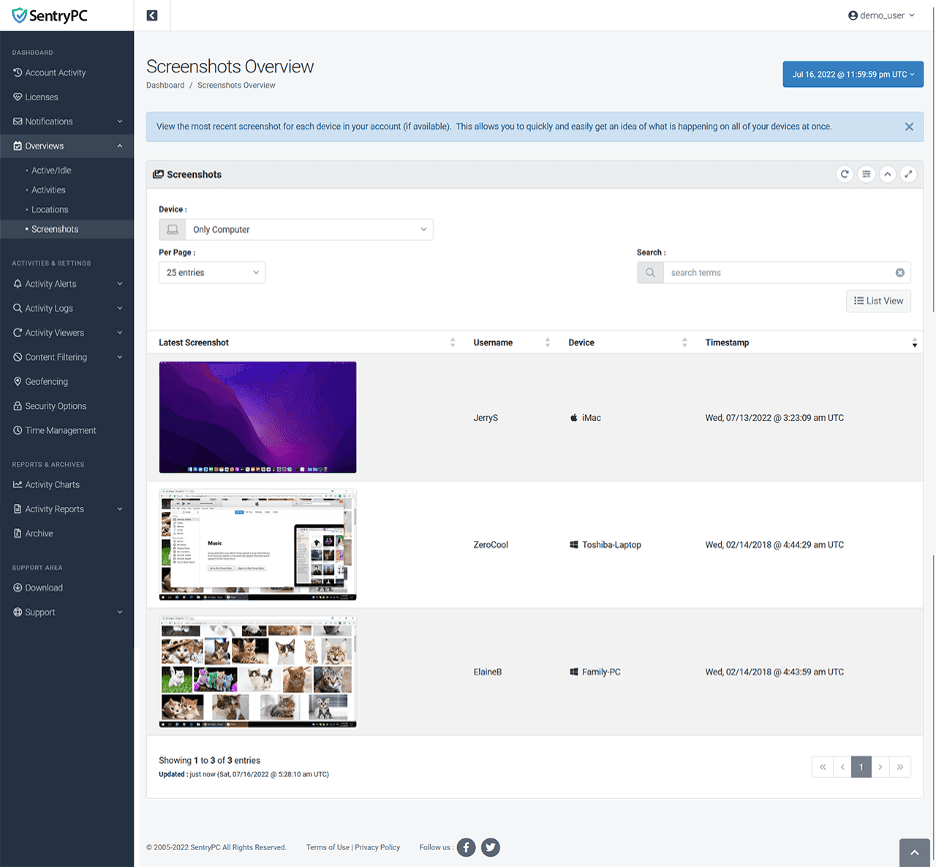
At the other end of the spectrum, platforms like Teramind and Controlio offer significantly deeper surveillance capabilities, including continuous screen recording, keystroke logging, keyword-based alerts and detailed user behavior analytics. These tools are typically favored by organizations in regulated industries like finance, healthcare or government contracting, where data loss prevention and insider threat detection are genuine operational priorities, not just nice-to-haves. The trade-off is that deeper monitoring requires more storage, more administrative oversight, and a much more carefully constructed internal policy to avoid creating a culture of distrust.
Consider privacy and ethics.
The ethical dimension of employee monitoring has moved from a background concern to a front-and-center decision factor, particularly as remote and hybrid work have normalized the presence of tracking software on personal devices and home networks.
Jen Seran, director of business operations at Stallion Express, implemented employee monitoring software with an eye on these realities. She suggests building on this employee buy-in by balancing functionality and employee comfort since monitoring should enhance productivity, not hinder trust.
“Choose a tool that your team can adapt to without feeling micromanaged,” said Seran. “The right software will ultimately help your business thrive while keeping your team engaged and empowered. After all, a motivated team is the backbone of any successful operation.”
Tools like WorkTime have carved out a niche by deliberately positioning themselves as non-invasive, emphasizing aggregated productivity trends, summary-level reports, and team-wide patterns rather than individual keystroke logs or screen captures. This approach reflects a growing recognition that monitoring can achieve its business objectives — identifying workflow bottlenecks, flagging disengagement, validating time allocation — without requiring the kind of surveillance that makes employees feel like suspects.
Beyond the tool itself, the ethical calculus also involves transparency, consent and legal compliance. Jurisdictions vary significantly in what they require employers to disclose about monitoring practices, and even where the law is permissive, organizations that deploy invasive tracking without clear communication risk damaging morale and eroding trust in ways that undercut the very productivity they’re trying to measure. The best practice is to match the monitoring depth to a clearly articulated business need, communicate that rationale openly to employees and select a platform whose feature set aligns with where your organization wants to sit on the spectrum between insight and intrusion.
Test the platform’s usability.
You can purchase the best software in the world, but it will be a waste of money if your team doesn’t know how to use it effectively. Look for software that matches your monitoring needs and your employees’ tech capabilities.
For Seran, usability was one of the most important factors, including intuitiveness and cross-platform functionality.
“Our workforce uses a variety of platforms; thus, Hubstaff’s intuitive UI and cross-platform functionality were crucial,” said Seran.
Misty Spittler, founder of Insurance Claim Academy, agreed that choosing a user-friendly platform is vital.
“Choose software with an interface you understand,” said Spittler. “Complicated tools create more work, not less. And test extensively during the free trial to ensure the data and reports are actually helpful before committing long-term.”
Conduct a deliberate software deployment process.
Most modern employee monitoring platforms default to cloud-based deployment, and for good reason: cloud infrastructure offers faster rollout, automatic updates, easier scalability and minimal burden on internal IT resources. Tools like Time Doctor exemplify this model, allowing organizations to get up and running quickly across distributed teams without provisioning servers or managing on-site hardware. For many small and mid-sized businesses, cloud deployment is essentially the only practical option, and the reliability of major hosting providers has made security concerns around cloud storage far less acute than they were a decade ago.
That said, organizations with heightened security requirements may need on-premise deployment options that keep all monitoring data within their own controlled infrastructure. Some platforms offer this as an alternative or hybrid configuration, which provides greater control over data storage, access and retention policies at the cost of higher upfront investment and ongoing maintenance. The deployment decision should be driven by your organization’s regulatory environment, IT capacity and risk tolerance rather than defaulting to whichever option is easiest to set up.
Assess platform security.
Employee monitoring software can capture a wealth of information, which is why one of the most important features to look out for is platform security. When we spoke with David Weisselberger, founding partner at Erase The Case, he confirmed this to be true for his business.
“Adherence to legal business norms and data encryption were the two most important variables [for us],” Weisselberger told us. “It was vital to make sure that our clients’ private information was safe and secure. These worries were allayed by Hubstaff’s SOC 2 accreditation and HIPAA compliance.”
When you speak with an employee monitoring provider about their software, inquire about what security measures will be taken to keep your employee, client and company data secure.
Select a platform that suits your industry.
Not all workforces look the same, and monitoring tools built primarily for desk-based knowledge workers often miss the mark for businesses with shift-based, hourly, retail or field operations. Platforms like Homebase are designed specifically for these environments, offering features like shift scheduling, time-clock functionality, team communication and basic labor cost tracking that align with how local and retail businesses actually operate day to day. For a restaurant, a retail chain or a home services company, the value of a monitoring tool isn’t in screen recording or keystroke analysis, but in knowing who’s clocked in, whether shifts are covered and how labor hours map to revenue.
Choosing an industry-aligned platform also reduces adoption friction. Employees in shift-based roles are generally accustomed to punching a clock, so a tool that digitizes and streamlines that familiar workflow feels like an operational upgrade rather than surveillance. Conversely, deploying a feature-heavy enterprise monitoring suite in a retail environment is likely to create confusion, waste budget on capabilities nobody uses and potentially alienate a workforce that doesn’t sit in front of a computer all day. The key is to start from how your business actually runs and select a platform whose core feature set was designed for that reality, rather than retrofitting a tool built for a different kind of organization.