To run a successful business, you must ensure data and network security, comply with all applicable industry and legal regulations and help your team be as productive as possible. User activity monitoring (UAM) technology can help with all three facets. However, these tools require thoughtful implementation and careful oversight. We’ll explain the benefits of UAM and share best practices for selecting and implementing the right UAM technology in your organization.
What is UAM?
UAM is the practice of tracking and recording users’ digital activity, typically in an organizational environment. Software and other tech tools facilitate UAM to help employers ensure security, maintain legal compliance and boost business productivity.
UAM can be used to track systems as small as individual company-owned devices (e.g., desktops, laptops, cell phones) or as large as entire networks. Employers can set the scope of how detailed monitoring will be, depending on their size, industry and security needs.
“The purpose behind the monitoring is to maintain security, whether that be a network intrusion, the theft of sensitive information or other threats,” explained Michael Trust, human resources director at Myman Greenspan Fox Rosenberg Mobasser Younger & Light LLP. “UAM is used to monitor threats from internal actors, as opposed to an external threat, which is a different type of security.”
Editor’s note: Looking for the right employee monitoring software for your business? Fill out the below questionnaire to have our vendor partners contact you about your needs.
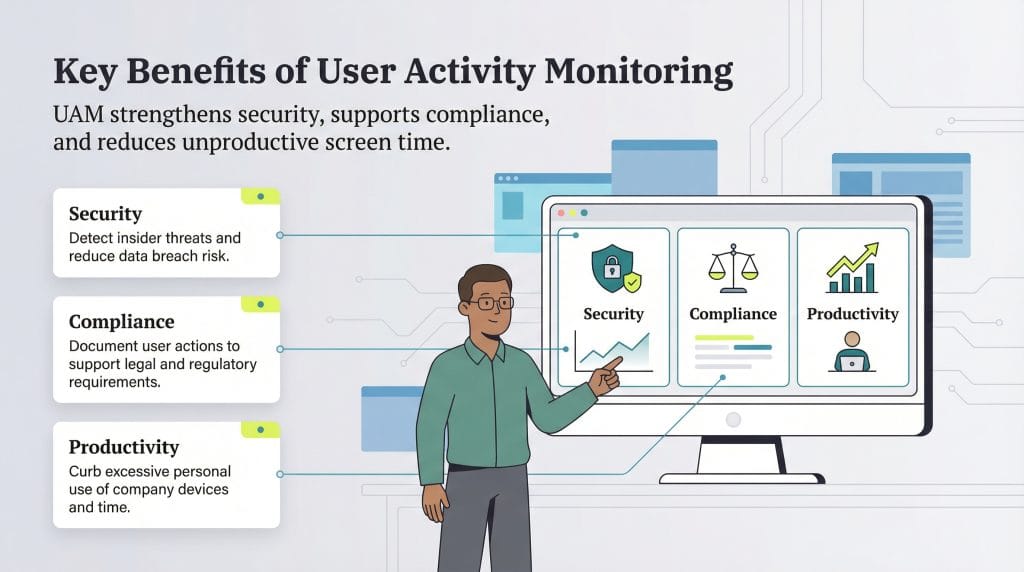
What are the benefits of UAM?
Real-time monitoring of employee behaviors and actions brings three primary benefits to a business: maintaining network and data security, ensuring legal compliance and protection and improving employee productivity.
Security
UAM is typically part of an organization’s cybersecurity plan, with tech tools designed to:
- Secure networks and devices
- Reduce the risk of data breaches
- Protect proprietary information and trade secrets
- Prevent data loss
While firewalls and anti-malware tools help keep out malicious intrusions, UAM tools protect the company from within. For example, they can prevent malicious employees from sharing proprietary information with unauthorized users or uploading malware to networks or devices. They also help guard against innocent mistakes, such as users unintentionally accessing harmful web content.
UAM tools monitor security threats in real time and create an audit log, allowing your information technology (IT) or security team to address them promptly.
Legal compliance and protection
Some employers rely on UAM solutions to maintain legal compliance and protect their organizations against litigation. For example, highly regulated industries like healthcare and financial services tend to have strict guidelines on what types of information can be shared and with whom. Tracking user behavior in real time helps companies ensure that users comply with those laws and regulations.
Additionally, if a specific user engages in illegal activity, such as theft, gambling or harassment, on your network or devices, you can identify it and take appropriate disciplinary action quickly.
These surveillance tools track user actions in real time and can store and report on historical activity, helping your business protect itself in the event of business lawsuits filed by disgruntled employees or customers.
Employee productivity
Tracking user activity can potentially increase employee productivity by limiting time spent using company devices for personal use.
“A very common example is monitoring of employee access to social media for personal use on company time and using company IT resources,” explained David Miller, labor and employment attorney at Bryant Miller Olive. “If employees know they are monitored, they are deterred from wasting paid time on unproductive activities.”
Although some employees may view monitoring software as a sign of employer distrust, you can mitigate this concern by discussing your monitoring policies with your team and explaining the reasons behind them.
Is UAM legal?
Yes, in most U.S. states, employers can legally monitor employee activity, but there are important rules to follow. Federal and state laws vary, so businesses must stay informed to remain compliant. Stay mindful of the following:
- Federal law: At the federal level, the Electronic Communications Privacy Act allows employers to monitor electronic communications, like email or phone calls, as long as there’s a legitimate business reason or the employee gives consent. However, the law also protects against unauthorized interception of private conversations.
- State laws: Some states take things further. For example, California, Connecticut, Florida, Louisiana and South Carolina have stricter rules. These may include requiring two-party consent for recording conversations or written notice before monitoring. Other states, like Delaware and Illinois, also have specific consent or notice requirements.
- What is being monitored: What’s allowed depends on what you’re monitoring, such as email, web activity, video and GPS, whether employees are informed and personal devices or off-hours activity are involved. Without clear notice — especially in remote work settings — overly aggressive monitoring could cross a legal line or, at the very least, damage employee trust.
To stay on the safe side, be transparent. Include clear monitoring policies in your employee handbook. Spell out what’s being monitored (for example, if you’re monitoring employee cell phones), how the data is used and whether personal devices are included. Also, ensure you follow applicable data privacy laws, like the California Consumer Privacy Act.
When in doubt, check with legal counsel to ensure your policies meet both federal and state standards.
An
acceptable use policy can complement your monitoring efforts by outlining what employees can and can't do on company devices, helping set expectations and keep everyone on track.
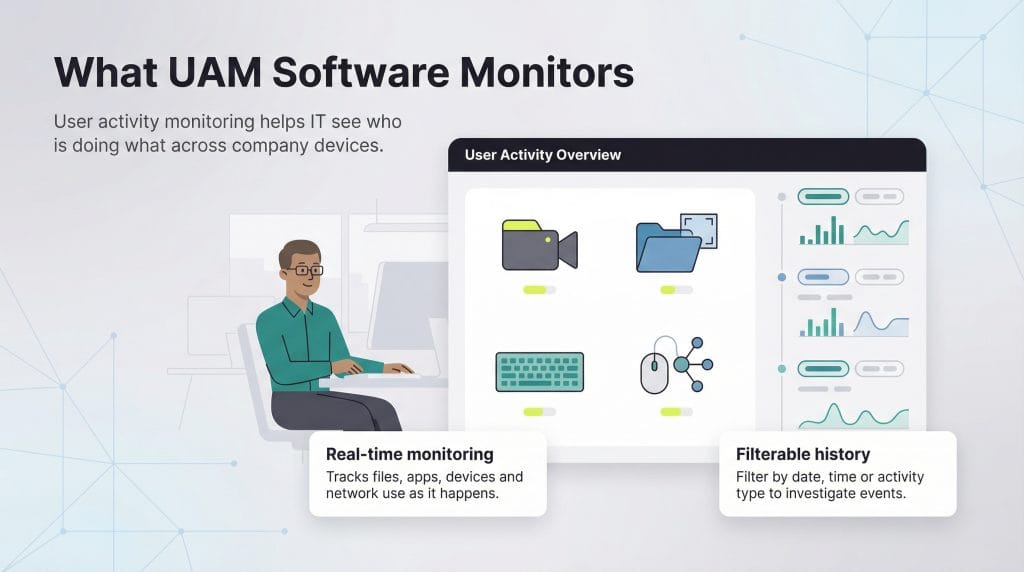
What does UAM software do?
UAM tools and capabilities differ and can include the following functionality:
- Recording video for surveillance
- Capturing files and screenshots
- Logging keystrokes
- Tracking mouse, keyboard and network activity
“UAM software reviews in real time what files, applications, devices, servers, networks, websites, internal drives, external drives, etc., are being accessed, what is being accessed and by whom,” Trust explained. “It can also show if and what documents are being uploaded and downloaded during this review.”
UAM data is typically recorded in real time but can be filtered by date, time or file type to help IT teams quickly find what they need.
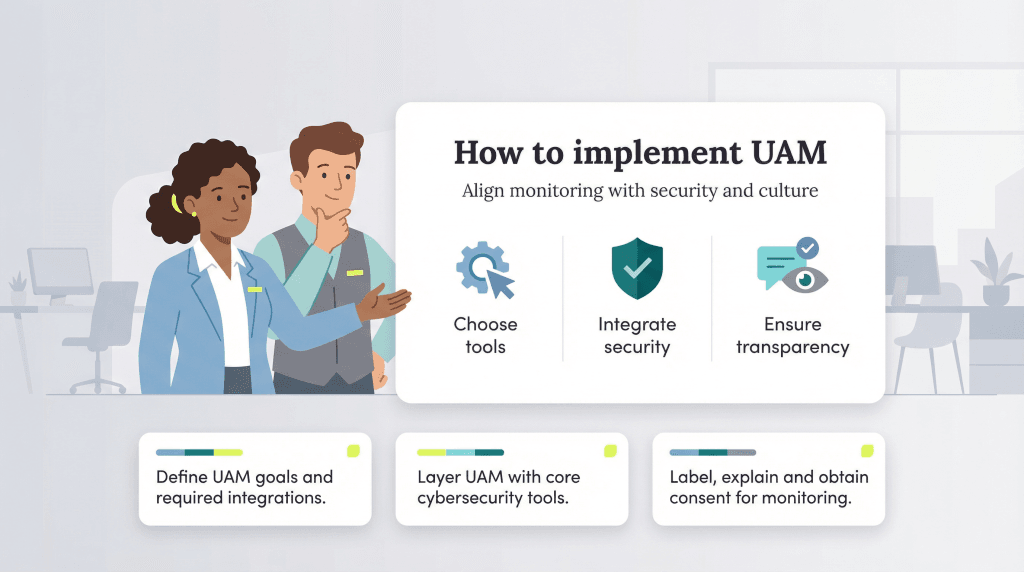
How should you implement UAM?
To create and implement a successful UAM policy, choose the right tools, emphasize security and disclose all monitoring processes to your employees.
Choose your UAM software carefully.
No single platform or tracking tool will suit every business’s monitoring needs. Before choosing a platform, identify your needs:
- Do you want to track user activity to maintain cybersecurity?
- Is employee productivity your top priority?
- What software should your UAM tool integrate with?
“Define your needs and objectives and then choose a software that meets them,” Miller advised. “Only choose software that can integrate with your other platforms, like data security systems.” (We highlight several options below.)
Incorporate UAM into your cybersecurity plan.
UAM software can be a powerful security tool, but it’s not enough on its own. Trust recommends using UAM tools along with other strategies and safeguards to protect your business from cybercrime and data loss, including the following:
- Antivirus software
- Multifactor authentication
- Fewer shared accounts
- Strong passwords
- Frequent password changes
- Strict file-sharing procedures
Access control is also a huge part of protecting your business’s sensitive information. Some companies mistakenly give all employees access to confidential data, even when it’s not necessary for their roles.
“Many organizations do not lock down this information and so employees could freely, for example, obtain a confidential customer list or product design or financial information or payroll information and share it maliciously inside and/or outside of the organization,” Trust said. “It could also be shared innocently for gossip. In either case, it’s a security threat.”
Using a combination of UAM and other cybersecurity tools gives your business a stronger defense against potential threats.
Openly disclose UAM policies to employees.
Even if you’re not legally required to, it’s important to tell employees you’re monitoring them. This transparency can ease concerns about trust while reinforcing your expectations around privacy and security, and it helps you avoid violating employee rights through undisclosed surveillance.
“User activity monitoring has ‘invasion of privacy’ implications,” Miller cautioned. “Employers should be careful to eliminate any expectation of privacy employees might have in, for example, personal emails, personal documents stored on company computers or social media use.”
After discussing your monitoring policies with employees and answering any questions they have, obtain their consent with a signed acknowledgment. You should also add your monitoring policies to the employee handbook.
UAM works best as part of a cybersecurity plan in organizations with a healthy company culture. For best results, communicate with employees about their activity, recognize high performers and create
performance improvement plans for those who need support.
What is the best UAM software?
Monitoring software can vary significantly. The best employee monitoring software for your business will depend on your unique situation and goals. Here are a few excellent options to consider:
- Teramind: If security is your top priority, Teramind is a powerhouse at protecting your business. The software is easy to navigate, with an online demo and installation assistance. It offers advanced security and compliance tools, screen recording, keystroke logging, Health Insurance Portability and Accountability Act compliance reporting and 24/7 tech support. Read our full review of Teramind to learn more.
- ActivTrak: ActivTrak is a good option if your primary goal is managing and improving employee performance. The software provides essential, easily digestible data that can help business owners make informed decisions while improving employee productivity and work-life balance. Our ActivTrak review details this platform’s productivity features and more.
- InterGuard: InterGuard is a solid UAM solution that may be particularly helpful if you have a remote work plan. The platform keeps data secure across multiple devices, whether you’re in or out of the office. See our comprehensive InterGuard review to explore its remote work features and security tools.
Julie Thompson contributed to this article. Source interviews were conducted for a previous version of this article.