Data tells us who our best customers are, which staff members perform well and how to improve efficiency in our businesses. Companies need this data to make the right decisions about their current and future direction.
But leaders must be sure that the information they’re working from is accurate, up to date, consistent and concise. Below, we explain what data integrity is and recommend five resources to help you improve data management and integrity in your business.
What is data integrity?
Data integrity refers to how reliable a database is throughout its life cycle. Essentially, it answers the question: Can the digital information your business relies upon be trusted?
For a database to have integrity, it needs the following five characteristics:
- Accuracy: The data a company uses should reflect reality and be free of errors. From a business perspective, inaccurate data leads to poor decision-making and operational issues.
- Attributability: It must be clear who has recorded new or altered existing data and when this was done to ensure accountability and traceability.
- Contemporaneousness: When someone enters new or alters existing data, the addition or change must be recorded in the database immediately.
- Legibility: Entries should conform to notation protocols (in other words, people should add or amend data using the same set of instructions) so that others can understand them. Where information is corrected, the reason for the change must be given.
- Originality: Data should remain in its original form without alteration. Any necessary changes must be recorded separately to maintain the integrity of the original data.
Types of data integrity
There are two types of data integrity: physical integrity and logical integrity.
Physical integrity refers to who has access to data. Data can be stored either on hardware, including cloud computers and/or removable media like flash drives and DVD-ROMS.
To achieve physical integrity, your data must be retrievable immediately following an event, such as flooding, extreme weather, device failure, cyberattack and connectivity and power outages. [Related article: From COVID-19 to Hurricane Season: Disaster Preparedness for Small Business]
Logical integrity requires the following four characteristics:
- Entity integrity requires a primary key, which is the unique identifying ID on every database column row/record.
- Referential integrity requires a foreign key, which is a shared reference linking a record on one database to another. For example, an “order number” foreign key may feature on both a customer relationship management (CRM) record and a dispatch record. A change on the CRM record will not change the dispatch record which uses the same foreign key.
- Domain integrity is a way of validating data in a database column (for example, the presence of an “@” sign and a recognized top-level domain (TLD) for email address data).
- User-defined integrity are extra fields, unrelated to the other three, where additional information is stored.
Data strategy consultant Caroline Nesbitt told us that, “ensuring logical integrity is particularly challenging for organizations with siloed systems or fragmented processes as these can lead to inconsistent or conflicting data.”
Nesbitt highlighted that overcoming these challenges starts with ensuring that your databases can share information smoothly. “Managing your metadata and validating your data throughout its life cycle will improve your overall data quality,” she added. “With the right data governance practices, your data relationships remain accurate and consistent across departments.”
Why is data integrity important?
Data integrity, or the lack of it, has an impact across every area of business. With approximately 80 percent of data migrations failing to achieve their business objectives because of data quality issues, it is essential to use accurate and complete information. Eight key benefits data integrity delivers are:
- Better decision-making: The more accurate the data, the clearer managers can see how well the business is doing and where improvements are needed. Good data helps businesses find ways to cut costs, work more efficiently and expand into new markets.
- Accurate customer information: With accurate client data, marketing teams can personalize promotional communications and sales teams can tailor their pitching based on actual customer profiles and preferences. Customer service teams are also better able to respond to inquiries with the correct records in front of them.
- Easier data accessibility: Centralized, reliable and well-maintained data allows employees to find and use the information they need quickly. This also leads to greater collaboration between teams and departments.
- Greater efficiency: Inaccurate data results in employees spending time and money identifying and fixing mistakes. Conversely, accurate data frees up staff to focus on performing higher-value tasks, improving profitability.
- Regulatory compliance: Unorganized data puts companies at risk of violating legislation like the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). Persistent failure to follow data laws puts companies at risk of legal action by regulators and consumers.
- Reputational benefits: Customers want to feel that the data you hold on them is accurate and safe. When it is, that builds consumer trust and makes each of their interactions with your company more personal.
- Enhanced security: Although data integrity is not directly related to cybersecurity, it makes spotting unauthorized changes and suspicious activities like unauthorized logins and data breaches more detectable.
- Improved data integration: Having a central source of information that approved apps and tools can access and update reduces the costs of managing multiple systems and the need to handle duplicate data.
Nesbitt emphasized that “data integrity is not just a regulatory requirement; it’s a strategic imperative for modern businesses. By prioritizing accurate and consistent data, organizations enhance decision-making, drive operational efficiency and foster customer satisfaction.”
She advised that poor data quality can undermine key business initiatives and prevent companies from staying competitive, stating, “High-quality data is essential for leveraging emerging technologies like AI [artificial intelligence] and machine learning, which rely on well-governed information to provide reliable insights. Investing in data integrity creates a strong foundation for innovation and long-term growth, positioning businesses to thrive in the digital age.”
Common threats to data integrity
The most common threats to data integrity are:
- Lack of perceived importance: Maintaining data integrity needs to be a core business process driven from the top whose importance needs to be clear to all.
- Absence of processes: You need processes to determine how data is being entered into and altered on your system, what data is recorded and who’s responsible for recording data. Many companies use workflow diagrams that show data input and output and all of the changes that might occur in between.
- Insufficient auditing: Regular data sweeping using validation and auditing tools to find errors quickly. It can also uncover data disparities in systems and processes.
- Overly broad data access: Staff should only be able to access the data they need to do their work. If their log-ins are compromised, this restricts what data a hacker can access by default.
- Inadequate user training: You need to invest in employee training to ensure that all database users (including contractors) know how to correctly record and alter data. This greatly reduces the chance of mistakes and incorrect formatting. That won’t eliminate all human error but it will reduce it.
- Missing data backups: Internal and external bad actors threaten the security and privacy of your data. You need to make regular use of top online cloud storage services to back up your database to protect against this as well as any data loss from preprocessing errors or hardware/software failure.
- Weak cybersecurity: Companies should identify which data is of the greatest value and run a cybersecurity audit to determine how best to protect it. [Related article: A Cybersecurity Plan for Small Business Owners]
- Poorly configured hardware and software: When selecting new hardware or software, you should make sure that it will work with existing technology and requires little or no configuration. Companies should ensure software patches are downloaded on the day of release and retire software that is no longer being supported by a vendor.
From the above list of threats, Dr. Ryan Ries, chief AI and data scientist at cloud services provider Mission Cloud, mentioned the absence of process as a particular danger. He told business.com, “One issue we often see with our customers is that they often lose accuracy and originality. Many customers allow their employees to pull data into visualization tools and slowly but surely create more and more ETL [extract, transform and load] processes in that tool.”
He explained that once the data is no longer controlled by your processes, the accuracy disappears as everyone makes slight changes in their ETL causing people to have different results.
Nick Barter, co-founder and chief strategy officer of Nothreat, is also concerned about who has access to data in an organization. He stated that, “even small, unnoticed changes to data can have catastrophic long-term consequences. These subtle changes to key data can, over time, build up to become major problems in areas like financial reporting, inventory management or security configurations.”
How to ensure data integrity
Now that you understand why data integrity is so valuable for companies, it’s time to learn how to achieve it. When stakeholders and executives are confident in their data, they can move forward more aggressively with plans and growth.
Most big companies gather data through numerous approaches, including the following:
Plenty of companies use a combination of these data collection methods. But what can you do to ensure data integrity? Here are some ideas:
- Management: Make sure your business’s management understands the significant role data integrity plays in your daily operations.
- Delegation: Assign clear functions and duties to ensure everyone takes responsibility for maintaining data integrity.
- Systems, processes and screening: Front- and back-end systems are mostly responsible for data collection, but you also need a process to establish how data is being entered into these systems. Most companies use workflow diagrams that show data input and output and all of the changes that might occur in between.
- Policies: Many companies are now establishing and executing policies demanding the regular examination of data. One common practice is to create data integrity reports that focus on data disparities in systems and processes. Such reports can help companies proactively address data issues.
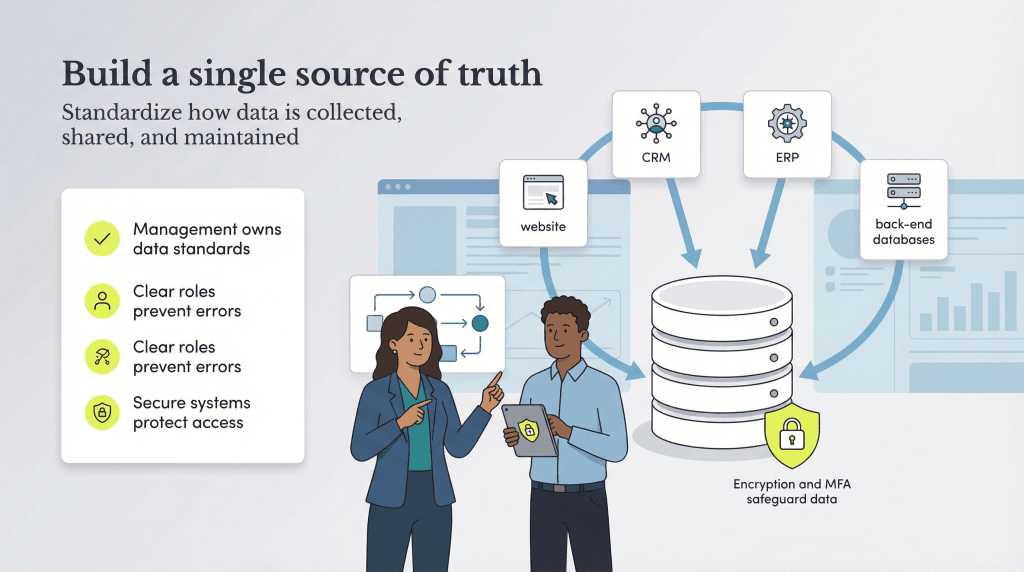
Nesbitt highlighted that many companies have problems with data integrity because of systems and databases that don’t integrate and poor internal practices. She said that companies should take a proactive approach to digitize data collection to remove the threats of manual errors and data silos and to establish a single source of truth in a business: a centralized database that connects to all the software a firm uses.
Kunal Madan, co-founder of Amarra, told business.com that he’d seen firsthand how discrepancies and inaccuracies cause serious consequences, especially when dealing with high-net-worth investments and online retail. “One effective approach is to take a comprehensive data governance strategy, which encompasses clear policies, role-based access control and stringent auditing processes,” he said. “You need to implement strong cybersecurity measures, including the use of advanced encryption and multi-factor authentication, to protect against unauthorized access or breaches.”
Data integrity practices help to stop CRM data decay meaning that, when you reach out to customers with new products and services, you won’t be working with out-of-date contact details.
Recommended resources for managing data integrity
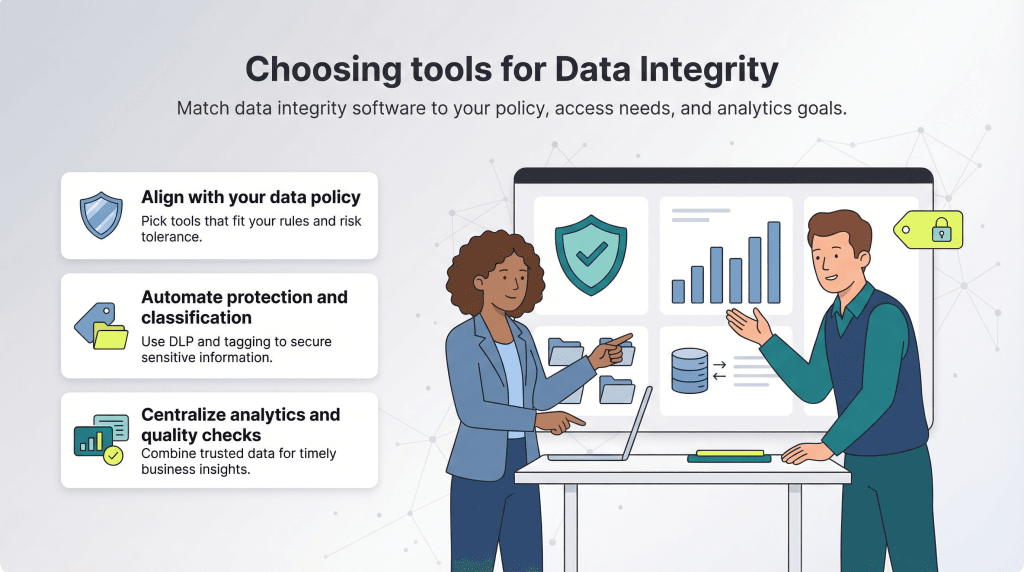
There are a number of data integrity management tools available. Make sure that you choose the one whose core set of features best matches the data integrity aims and policy you create for your business.
Here are a few options to consider.
1. Digital Guardian data protection
Digital Guardian, part of Fortra, provides data loss prevention (DLP) that protects your sensitive information from both internal and external threats. You can keep track of who accessed your data and what they did with it allowing you to respond quickly to breaches and you can ensure stakeholders that reports are drawn from data that was not altered in inappropriate ways.
2. Varonis data classification engine
Varonis offers a variety of data management solutions, including a classification system that automatically identifies sensitive information. For organizations that have multiple levels of access, this can reduce the resources needed to safeguard information significantly while keeping data available for appropriate business use.
3. Explorance employee experience surveys
Explorance helps companies gather accurate data and analyze it for decision-making purposes via its Blue platform. You can use it to poll between 100 and 200,000 people within your organization.
4. Panoply data management tools
Panoply collects and combines disparate data, housing it in a single, catch-all cloud data warehouse and AI-driven integration platform that can be queried for analytical purposes. Panoply makes it easier to get a clear, big-picture analysis from a variety of sources, including marketing surveys, industry reports and internal sales figures.
5. Ataccama ONE smart data curation platform
Ataccama ONE is a cloud-based, on-premises and desktop platform that brings data together and offers analysis guidance via smart profiling. This is in addition to its core automated data collection and curation functionality.
Whether you opt for a resource from this list, find another software program that meets your needs or decide to develop something in-house, if your data isn’t accurate and timely, your business will suffer. So, take the necessary steps today to ensure data integrity is a high priority for your company.
Source interviews were conducted for a previous version of this article.