Cybercrime is getting more sophisticated — and expensive. Cybersecurity Ventures estimates global cybercrime costs could approach $12 trillion annually by 2030. That kind of exposure is hard to ignore, especially if your systems still rely on passwords alone. Adding multifactor authentication (MFA) is one of the simplest ways to help protect your business. MFA doesn’t replace passwords; it adds another step before access is granted. And that extra step can make all the difference: Microsoft reports that 99.9 percent of compromised accounts lacked at least one additional verification method.
Authenticator apps power that second layer. They generate one-time passcodes users must enter before accessing company accounts or systems, helping prevent stolen credentials from turning into full-scale data breaches. We’ll explore six top-rated authenticator apps to help you choose the best fit for your business. Many are part of broader identity management platforms, which may also be worth considering, depending on your security needs.
If usernames and passwords are your only defenses, your business is vulnerable. Authenticator apps add a critical layer of protection against phishing,
ransomware attacks, malware and other
cybercrime threats.
1. Twilio (Authy and Verify)
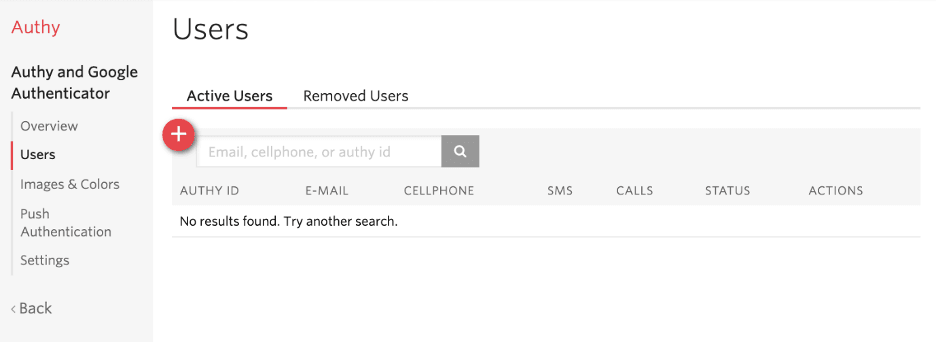
View active and removed users at any time through the Authy dashboard. Source: Twilio
- Price: Starts at about $0.05 per successful verification request (plus small extra fees for things like text messages, depending on the country and method). Volume discounts are available.
- Compatibility: iOS and Android mobile apps (Authy); API integrations for web and mobile platforms (Verify).
Businesses can use Twilio’s authentication tools to secure employee logins and protect customer accounts. Authy is Twilio’s authenticator app for generating time-based one-time passwords (TOTP), while Twilio Verify powers SMS, voice, push and other verification workflows through its API.
Twilio’s usage-based pricing makes it attractive for businesses that prefer to pay per authentication event instead of per user. That structure can work well for companies with fluctuating login activity or seasonal spikes.
It’s also well-suited for e-commerce website security and subscription-based websites. You can require authentication when users log in from a new device, reset credentials or update payment details. Because pricing is tied to verification events, costs scale with actual usage, helping you control your cybersecurity budget. Think of it like paying for postage only when a letter is successfully delivered, not for every envelope you buy.
Twilio Authy/Verify features
Twilio’s flexibility is one of its biggest strengths. Businesses can customize how authentication works and choose from multiple verification methods, including:
- SMS text messages
- Voice calls
- Push notifications
- WhatsApp
- Time-based one-time passwords (TOTP)
- Passkeys
Other notable features include:
- International coverage: Twilio operates in more than 180 countries, making it suitable for global organizations.
- Developer-friendly platform: Ready-made libraries are available for Node.js, Python and PHP, along with detailed documentation.
- Scalable pricing and infrastructure: Start small and increase verification volume as your user base grows.
- Silent Network Authentication: Verifies phone numbers behind the scenes so users don’t need to enter a one-time password.
- PSD2 compliance: Supports Strong Customer Authentication (SCA) requirements for businesses selling to or accepting paid subscriptions from customers in the European Union.
2. WatchGuard AuthPoint
WatchGuard regularly updates its AuthPoint software for different platforms. Source: WatchGuard
- Price: Charged per user through an annual subscription. Contact WatchGuard or an authorized partner for current pricing, as rates vary based on subscription tier and user count.
- Compatibility: iOS and Android mobile apps; Windows and macOS (browser-based access)
WatchGuard AuthPoint is an authentication platform that helps secure logins to corporate computers, VPNs and cloud applications. It’s part of WatchGuard’s broader cybersecurity ecosystem, which includes firewalls, patch management, DNS-level protection and secure business Wi-Fi.
We like how the centralized dashboard lets IT teams manage AuthPoint alongside other WatchGuard services. Instead of switching between separate tools, administrators can control authentication policies from one place. From the dashboard, you can define which verification steps users must complete and configure features like single sign-on (SSO). With SSO enabled, employees can access multiple applications — such as Zoom and Salesforce — with one login instead of juggling separate passwords.
AuthPoint is a strong option for midsize organizations and businesses with distributed teams that need consistent security controls across locations.
WatchGuard AuthPoint features
- Multiple authentication methods: Users can verify their identity through the mobile app, time-based one-time passwords, QR codes and optional hardware tokens.
- Easy setup: Guided setup tools help administrators and end users get set up without extensive technical training.
- Customizable security rules: Create risk-based policies, such as requiring additional verification when someone logs in from an unfamiliar device or location.
- Mobile device DNA: AuthPoint identifies trusted mobile devices using unique attributes, helping block attempts from cloned or tampered devices.
- Offline authentication: Employees can still log in when they don’t have an internet connection, which is useful for remote or traveling staff.
- Broad integration support: AuthPoint connects with a wide range of business applications and network resources, reducing the need for custom development.
Alongside MFA, many small businesses are adding
biometric authentication — including fingerprint and iris scanning — to their security systems to reduce unauthorized access.
3. LastPass Adaptive MFA
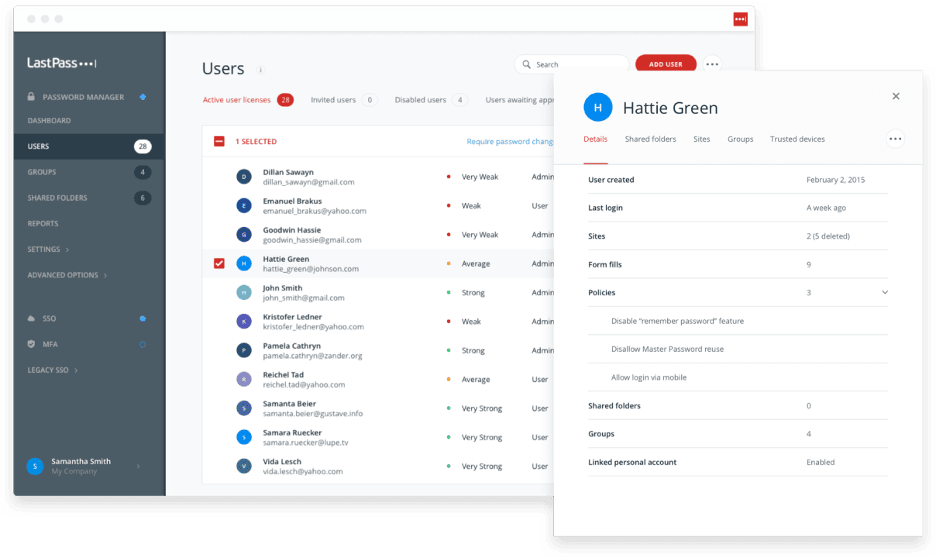
LastPass has a user-friendly interface and an intuitive control panel. Source: LastPass
- Price: Included in LastPass plans. The Business tier costs $7 per user per month (billed annually) and includes advanced MFA features such as VPN support, on-premises MFA and passwordless authentication.
- Compatibility: iOS and Android mobile apps; web browsers; supports hardware tokens
LastPass Adaptive MFA provides multiple authentication options to protect your company’s internal systems, cloud applications and business tools. Adaptive MFA is bundled with LastPass password management plans rather than sold as a standalone MFA product.
The platform includes the LastPass Authenticator app, which delivers one-time codes and push notifications for secure logins. You can also enable identity verification through device-based checks, biometrics (such as fingerprint or facial recognition) and hardware security keys, including YubiKey and Feitian devices.
We like the emphasis LastPass places on user experience. The platform is accessible to both technical and nontechnical employees. It also uses end-to-end encryption to help protect data in transit between users and LastPass’s servers.
LastPass can be a strong value if you want a companywide password manager with built-in MFA. However, if you’re only looking for a dedicated MFA solution, there are more affordable standalone options with fewer bundled features.
LastPass Adaptive MFA features
- Multistep protection: Combine multiple verification methods to add layers of security.
- Easy for employees: Whether using backup codes or fingerprint scans, authentication tools are designed to be quick and straightforward.
- Intelligent security checks: If a login attempt appears unusual — such as from a new location or at an odd time — the Authenticator app prompts for additional verification.
- Extended protection: Business subscribers can enable MFA for VPNs, workstations and on-premises applications.
- Security dashboard: View a real-time snapshot of your organization’s security posture, including security scores and accounts that require attention.
- User vaults: Each employee receives a secure vault to store and manage credentials in one place.
4. Cisco Duo Mobile
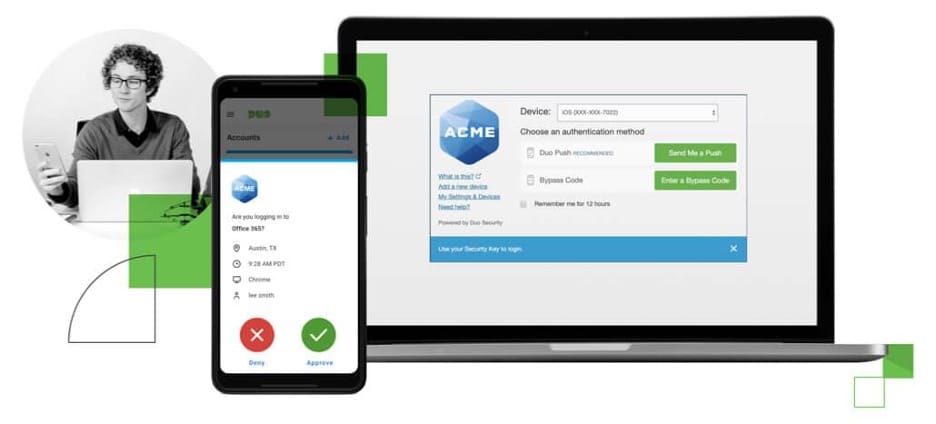
Cisco Duo is easily accessible across a variety of platforms. Source: Cisco
- Price: Free for up to 10 users; paid plans unlock additional features.
- Compatibility: iOS and Android mobile apps; Windows, macOS and Linux desktop apps
Cisco Duo is designed to simplify multifactor authentication. The apps download quickly and are straightforward for employees to use.
The admin interface is similarly easy to navigate. Whether you’re adding new users or defining which verification methods employees must complete to access corporate networks, cloud applications or VPNs, controls are centralized in one dashboard. Administrators can monitor device security at an individual level, configure SSO policies and enable biometric or passwordless authentication. The dashboard also shows who is logged in, which devices they’re using and whether those devices meet company security requirements.
Higher-tier plans include advanced features such as risk-based authentication, threat detection and zero-trust access controls. Duo is a strong option for businesses of all sizes that want robust MFA protection without an overly complex setup process.
Cisco Duo Mobile features
- Multiple verification methods: Duo supports push notifications, SMS codes, phone callbacks and hardware security keys.
- Strong phishing protection: Includes phishing-resistant options such as FIDO2 hardware keys and Verified Duo Push.
- Adaptive security: Prompts for additional verification when a login appears unusual, such as from a new location or outdated device.
- Device audits: Check whether employee devices are running current operating systems and security patches. Administrators can warn or block users who need to update.
- Wide integration support: Secure access to cloud platforms such as AWS and Azure, along with applications like Salesforce, SAP, Zoho and HubSpot.
- Free tier for small teams: The free plan for up to 10 users includes core MFA features and a built-in authenticator app.
If you're
setting up an online store, be sure to build in two-factor authentication to protect your customer accounts and business data.
5. Okta Workforce Identity
Okta users can easily view the apps they have access to. Source: Okta
- Price: From $6 per user, per month. Custom pricing for larger organizations.
- Compatibility: iOS and Android mobile apps; Windows and macOS (browser-based); supports MFA hardware
Okta’s Workforce Identity platform is a highly secure option for businesses that need to protect logins for employees, contractors and strategic partners. The Okta Verify authentication app is especially powerful out of the box; it connects to over 7,000 pre-built app integrations, covering both cloud-based and on-premises software. This can save IT teams a significant amount of setup time.
Okta Verify supports passcodes, biometrics, push notifications, one-time passwords and SMS and QR-based verification. One standout feature is FastPass, which can verify a trusted device and may eliminate the need for passwords entirely.
Okta is also known for its free password manager, which provides strong protection for individual accounts. But, for business use, we especially like the Workforce Identity platform, which represents a big step forward in user verification. A key advantage is adaptive MFA, which adjusts the level of verification required based on factors like user behavior, login location and device health. Organizations can also implement phishing-resistant technologies like hardware keys and smart cards as part of their MFA rollout — essential for defending against social engineering attacks.
Okta Workforce Identity is on the pricier side, but it offers a few standout capabilities, including workflow automation. For example, it can automate identity workflows and sync verified user data with connected systems like CRM platforms. It’s definitely worth shortlisting, though budget-conscious businesses may find better value with other platforms.
Okta Workforce Identity features
- Offline MFA backup: Team members can log in using offline passcodes when internet access is limited or unavailable.
- User directory: Store user information in a central location to streamline access and strengthen security.
- Simplified user life cycle: Automatically onboard new hires, manage permissions and remove access promptly when employees, contractors or partners leave.
- Device access management: Protect company data by limiting access to approved devices, apps and internal resources.
- Centralized user management: Manage users, groups and permissions from a single dashboard to simplify administration.
- Privileged access management: Securely control and monitor access to administrator and high-risk accounts across critical systems.
6. RSA SecurID
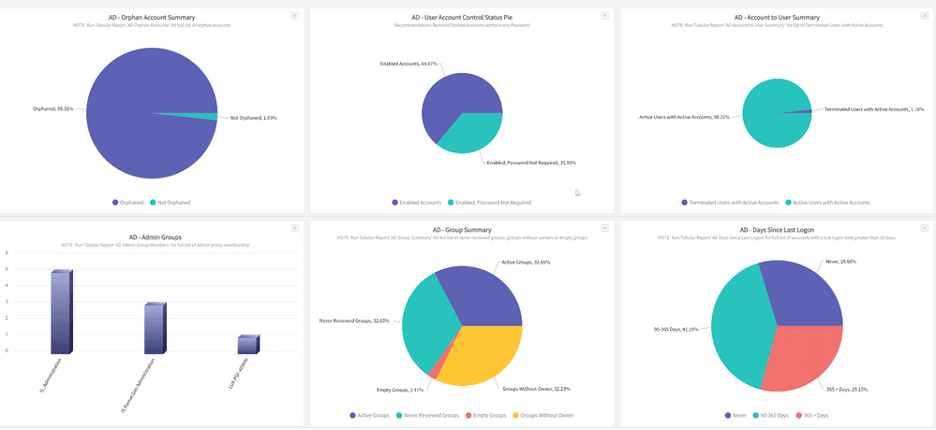
Get real-time analytics on all aspects of network security, including access attempts. Source: RSA
- Price: Contact the company for pricing.
- Compatibility: iOS and Android mobile apps; Windows and macOS (browser-based); supports MFA hardware
RSA SecurID offers strong protection for businesses with on-premises, hybrid and multicloud environments. Through the RSA Authenticator app, users can log in using various methods, including FIDO passkeys (mobile keys stored on smartphones or security keys), biometric verification, QR codes, one-time passcodes, code matching and app-based push approvals.
We were impressed by the system’s intelligence. It learns user behavior and device patterns, helping reduce unnecessary login prompts while still triggering extra verification when something seems off. We also liked the platform’s strong offline capabilities and the robust support available through RSA and its global partner network.
This flexible, easy-to-use system is a smart choice for medium and large enterprises. However, the platform’s extensive feature set may be more than most SMBs need — and it may come with a higher price tag than they’re looking for.
RSA SecurID features
- Zero-trust security: SecurID verifies every login individually, continuously confirming each user’s identity as they move across systems and apps.
- Easy user management: IT teams or system admins can quickly add, monitor and remove users directly from the dashboard.
- On-premises installation option: Businesses running on-premises or hybrid environments can install the software directly on their own hardware.
- Flexible security policies: Set role-, location- and device-specific access rules to fit your organization’s needs.
- High-compliance hardware keys: RSA’s iShield Key 2 Series meets leading cryptographic standards, including FIPS 140-3, HOTP, PIV and FIDO2.