Cyberattacks on big corporations are certainly newsworthy. However, hackers frequently target small businesses in data breaches and other digital intrusions. Cybersecurity incidents can paralyze your business and destroy customer trust — and recovering can be expensive. To help prevent these devastating consequences, it’s crucial for businesses of all sizes to put cybersecurity safeguards in place.
Like many core business functions, cybersecurity incurs expenses. But how much should you budget for your company’s cyberdefenses? We’ll look at best practices for cybersecurity budget planning, outline cyberattack costs and share various types of cyberincidents to be aware of.
Why budget for cybersecurity?
Mark Cunningham-Dickie, senior incident responder at Quorum, cautioned that cybersecurity risks affect businesses of all sizes — not just the major corporations. “While you do see a lot of big names on data leak sites, it’s not that there aren’t SMBs [small and medium-sized businesses] in among them,” Cunningham-Dickie explained. “It’s just that SMBs are more likely to pay ransoms because they don’t have the reputation, the insurance, the war chests, legal advice and backing, the recovery mechanisms and, potentially, the regulatory oversight that the big players do.”
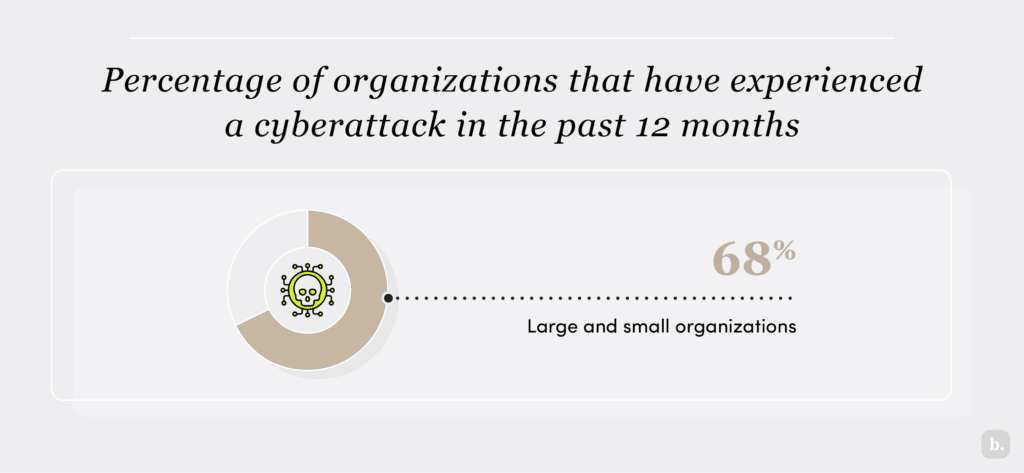
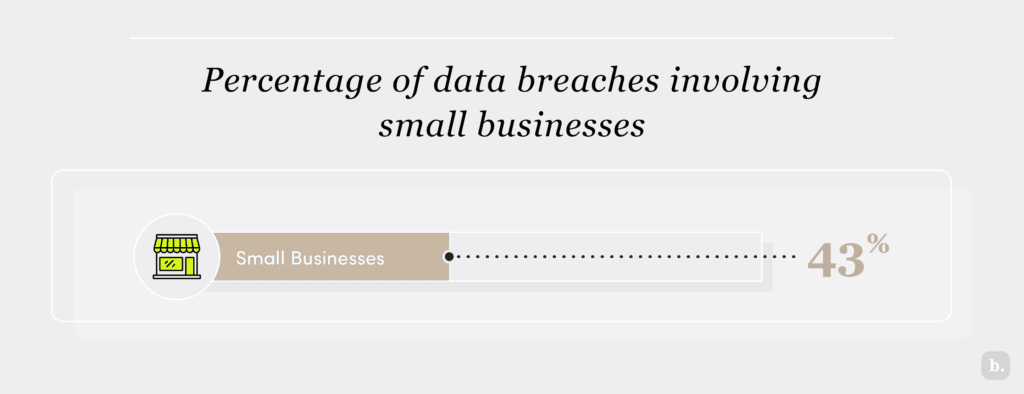
Indeed, small businesses are increasingly targeted. According to Netwrix Research Lab’s 2023 Hybrid Security Trends Report, 68 percent of all organizations surveyed — large and small — had experienced a cyberattack in the past 12 months. According to Tripwire’s recent Business Impact Report, 73 percent of small business respondents reported experiencing data breaches or cyberattacks within the previous year.
Here are some benefits of establishing a cybersecurity budget for your small business:
- Protecting your business: A cybersecurity budget funds programs that protect your company from a cyberattack’s costs and disruptions.
- Satisfying risk-assessment clauses: A funded cybersecurity plan acts as a safety measure for dealing with third-party cybersecurity risk assessments (or other vendor requirements). Risk-assessment clauses are becoming standard in contracts.
- Helping with compliance: Your cybersecurity budget will help you comply with regulations, such as the General Data Protection Regulation, Payment Card Industry Data Security Standard, Health Insurance Portability and Accountability Act and other national or state regulations, that legally require companies to maintain cybersecurity standards.
- Keeping your company competitive: Your cybersecurity budget will help you compete for large projects or contracts.
What cybersecurity areas should your budget include?
The cybersecurity arena is massive. As you build your budget, consider prioritizing the following investment areas:
- Risk assessment
- Business preparation and continuity
- Incident response
- Employee training
- Network and website vulnerability identification and management
- Regular scanning and testing, including dark web scanning and ethical hacking
- Cyber insurance policies
If you’re not convinced that your company needs a cybersecurity budget, consider that your business won’t be the only victim of a cyberattack; your employees, customers and strategic partners will also experience the fallout. The only way to prevent an attack is to strengthen your understanding, posture and defenses — a process that merits investment for every small business.
Cybersecurity risk management is the process of identifying the specific risks your company faces and planning how you'll defend against them. When you understand the risks, you can craft unique cybersecurity strategies to fit your situation.
How much should you spend on cybersecurity?
Cybersecurity spending is often tied to a business’s overall information technology (IT) budget, which takes into account the company’s size and IT infrastructure. According to the Spiceworks 2025 State of IT report, 64 percent of companies globally plan to increase their IT budgets for the following reasons:
- Increased security concerns
- Recent security incidents
- Updating older systems to shore up cybersecurity vulnerabilities
- Enhancing security software
- Spending more on managed security services
- Staying compliant with regulations
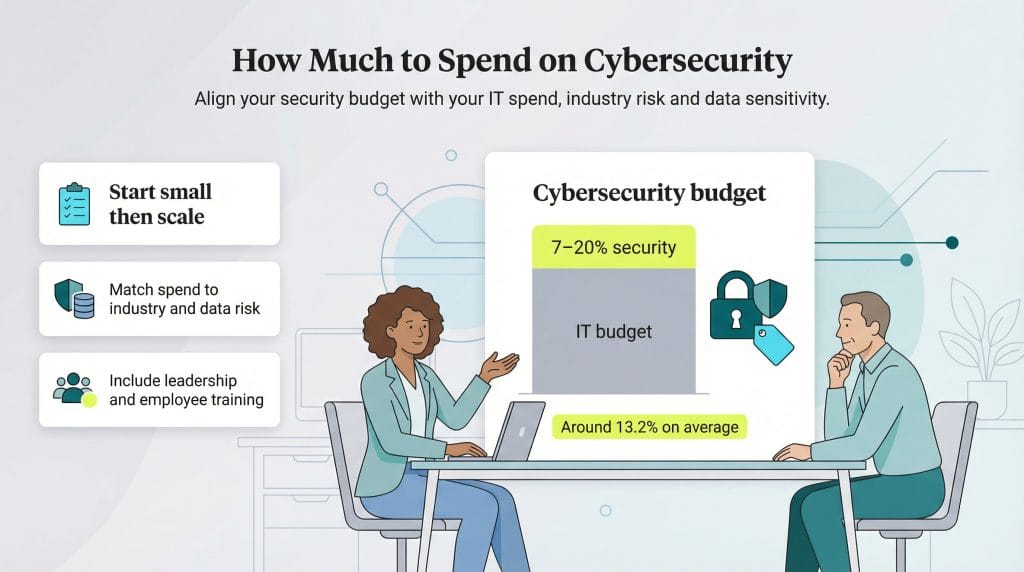
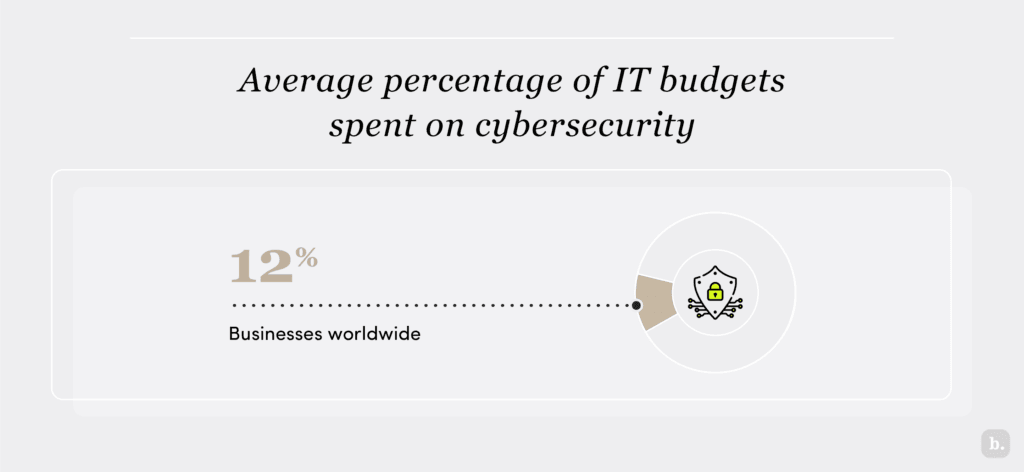
According to the 2024 Security Budget Benchmark Report, businesses globally spend an average of 13.2 percent of their IT budgets on cybersecurity. For example, if a company pays $3,000 monthly to an IT-managed service provider to cover its IT needs, its cybersecurity budget would be about $396 per month.
However, according to Ted Miracco, CEO of Approov, the exact percentage of total IT spending on cybersecurity will vary widely by industry, company size, compliance mandates, data sensitivity and more. “Different industries have varying benchmarks for cybersecurity spending, typically between 7 percent and 20 percent of the overall IT budget,” Miracco explained.
Miracco noted that defense contractors, technology companies and healthcare businesses tend to spend more of their IT budgets on cybersecurity, while manufacturing and retail industries spend less, averaging about 10 percent.
“The IT budget really should be a function of the actual data being stored or processed,” Miracco advised. “For example, financial, healthcare and personal data poses greater risks than other forms of data, and these data sources are most likely to be attacked by ransomware groups and/or nation-states.”
Best practices for smart cybersecurity spending
Here are a few tips for deciding on your cybersecurity spending:
- Don’t spend a lot all at once: When creating a cybersecurity budget, you don’t need to make a large upfront investment. If your business has never had a dedicated cybersecurity budget, start small and gradually incorporate it into your overall spending plan. A modest investment can go a long way. For example, with a relatively small budget, you can take the critical first step of conducting a cybersecurity risk assessment. This will help you identify vulnerabilities and prioritize key improvements without overwhelming your finances.
- Get advice from your cybersecurity provider: Your cybersecurity provider can help you identify your business’s highest-priority and lowest-cost action items. From there, you can tailor your cybersecurity program and slowly grow your budget to provide enhanced protection and mitigate risks. Your cybersecurity is an ongoing initiative, not a one-time project.
- Get company leadership on board: Small businesses often operate on tight budgets. In some cases, the person building and approving the budget may not understand the critical nature of cybersecurity. If you’re facing hesitation from leadership, stakeholders or the board of directors, perform a basic risk assessment to show them where your company stands and how an investment could bolster protection. Leadership — whether the board, C-suite executives or company owners — is responsible for guiding the company in the right direction and that includes protecting it from threats.
How much does a data breach cost?
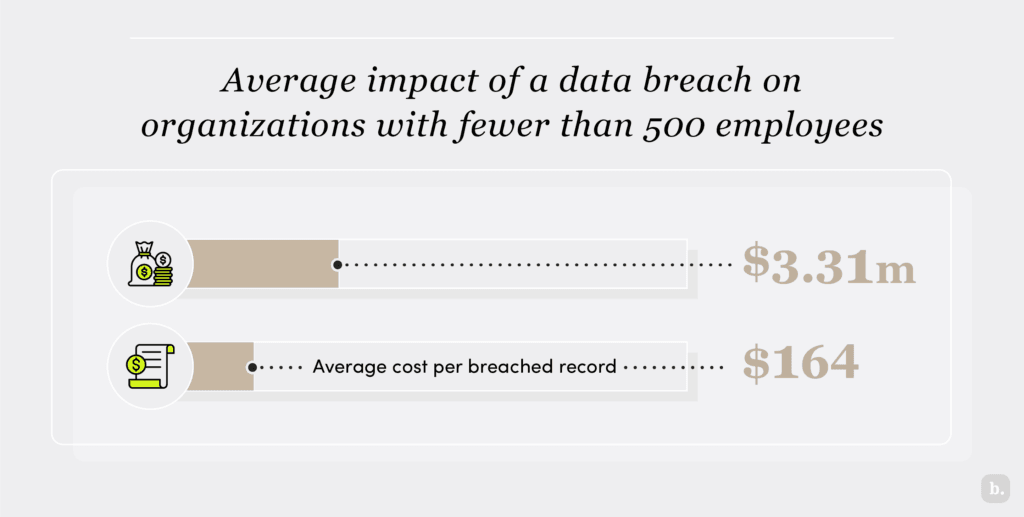
Cyberattacks cause significant damage and expense. According to IBM’s 2024 Cost of a Data Breach report, the global average cost of a data breach increased to $4.88 million, up 10 percent from 2023; the average cost per breached record was $173.
The true cost of a data breach isn’t always immediately known, particularly for small businesses.
Potential direct costs include the following:
- Monetary theft
- Remediation and system repair
- Regulatory and compliance fines
- Legal and public relations fees
- Notification, identity theft repair and credit monitoring for affected parties
- Increase in insurance premium
Potential indirect costs include the following:
- Business disruption and downtime
- Loss of business or customers
- Loss of intellectual property
- Damage to company credibility, brand and reputation
Taking crucial cybersecurity steps can mitigate the damage and reduce the costs resulting from a data breach. These steps include having an incident response team and cybersecurity plan in place, using encryption, conducting employee training and securing cyber insurance.
The concept of “cyberresilience” is growing in importance. Given the potential expenses and negative impacts of a data breach on a small business, any budget you dedicate to improving your company’s cybersecurity posture is well spent.
5 types of cyberattacks that threaten businesses
Your in-house IT team or outsourced IT partner should stay vigilant about the following cyberattack types. Some are obvious, while others are more overlooked attack vectors.
1. Denial-of-service (DoS) and distributed-denial-of-service (DDoS) attacks
A DoS attack is designed to overwhelm a machine or network’s resources so the intended users cannot access the system. It is executed by bombarding the specified target with a flood of traffic or information to crash the system.
Unlike other types of cyberrisks, DoS attacks do not directly benefit the attacker. For example, a competitor might initiate a DoS attack to disrupt your website and gain an advantage or the attack could serve as a diversion for a larger cyberthreat, such as ransomware deployment.
A DDoS attack is the same as a DoS attack but is launched from multiple host computers. This type of attack overwhelms a company’s website or online service, causing it to malfunction or become inaccessible.
There are different types of DoS and DDoS attacks, but here are the most common — and how to prevent them:
- TCP SYN flooding: These attacks exploit the TCP handshake process to overload a system. They can often be prevented by implementing rate-limiting or placing servers behind a firewall.
- Ping-of-death attacks: These attacks involve sending oversized packets to crash a target system. Placing your server behind a firewall and monitoring packet sizes can prevent these attacks.
- Teardrop attacks: Teardrop attacks result from a vulnerability that’s common in older versions of Windows; multiple patches have been issued over the years. Keep your operating system up to date to prevent teardrop attacks.
- Botnets: Botnets are networks of compromised computers used to launch large-scale DDoS attacks. Enabling RFC 3704 filtering, black-hole filtering, and monitoring for unusual traffic patterns can help prevent botnet attacks.
2. Phishing and spear-phishing attacks
Phishing attacks are a common cyberthreat in which attackers send emails that appear to be from trusted sources. The goal is to gain personal information, like usernames and passwords or to cause someone to take a specific action, such as downloading malware onto their machine.
A spear-phishing attack is similar, but instead of casting a wide net, attackers target individuals and take time to research victims and create personal, relevant messages.
The best way to prevent phishing attacks within your company is to train your staff on what to look for and how to spot risky emails and links.
3. Man-in-the-middle (MITM) attacks
As the name implies, an MITM attack occurs when attackers insert themselves between a user and the services they interact with. Common types of MITM attacks include session hijacking, IP spoofing, DNS spoofing and replay attacks.
No single method can prevent all types of MITM attacks. However, encryption and digital certificates help prevent attackers from inserting themselves between users and servers.
Additional safeguards include:
- Implementing strong authentication methods
- Avoiding unsecured public Wi-Fi
- Using virtual private networks to encrypt network traffic
4. Drive-by-download attacks
These attacks spread malware far and wide. An attacker looks for insecure websites to hack and plants malicious code throughout the site. When a user visits a hacked website, they may unintentionally download and install malicious code or be redirected to a site created by the attacker. Unlike other types of cyberthreats, a drive-by download doesn’t require the user to take an action, like clicking a button or opening an email, to be infected. They merely have to visit a website.
The best way to prevent this type of attack is to train your staff to keep their internet browsers and operating systems updated and avoid insecure websites. If your business manages its own websites, you should also implement robust website security practices, including regular updates and vulnerability assessments.
5. Password attacks
Obtaining a user’s password is among the oldest, most common and most effective cyberattack forms. Hackers can steal passwords in several ways:
- Watching someone type in their password
- Searching for unencrypted passwords on a network
- Using social engineering to reconstruct passwords
- Guessing a correct password through brute-force or dictionary attacks.
To protect your company from password attacks:
- Implement two-factor authentication policies.
- Require your employees to use strong, unique passwords.
- Implement a policy that locks user accounts after several invalid password attempts.
Cybersecurity spending is a small price to pay
Cybersecurity is no longer a “nice to have” — it’s a must-have item for businesses and a necessary budget item. A comprehensive cybersecurity program doesn’t have to cost a lot, but it requires prioritization and commitment from leadership, IT and other employees.
No matter how much you dedicate to cybersecurity, however, there are no 100-percent protection guarantees. Your best bet is to deploy a multifaceted, ongoing cybersecurity program using a combination of resources, testing, training and time.
Cunningham-Dickie emphasized that proactive cybersecurity efforts are key to reducing risks and deterring attackers. “The earlier you detect a threat and, the better you are at countering attacks, the less likely opportunistic attackers are going to have an impact on you,” Cunningham-Dickie explained. “They will just move on to the next potential victim.”
The cost of a comprehensive cybersecurity program is a small price to pay for the peace of mind you’ll enjoy knowing that your company is better protected.
Jennifer Dublino contributed to this article.