Big data is transformative because it provides entrepreneurs with valuable insights into their businesses. Coupled with artificial intelligence and machine learning, big data has the potential to deliver better marketing returns. It can also inform product development, increase efficiency, reduce excess inventory and prevent fraud.
However, big data comes with big risks, including exposure to hackers and other cyber threats. For this reason, many businesses are incorporating data minimization into their cybersecurity and risk management policies. We’ll explain data minimization, its benefits and how to implement it.
Many businesses store sensitive information in the cloud. Before signing up with a provider, ensure it uses robust
cloud data encryption technology to protect your data.
What is data minimization?
According to Cody Hall, product manager at Synology’s U.S. headquarters, data minimization is the intentional and responsible ingestion and retention of high-quality, useful information. “Ingesting any data and retaining it forever is unsustainable,” Hall explained. “Barring compliance requirements, all of your data should have a lifecycle planned out.”
In simplest terms, data minimization means:
- Keeping only the data your business needs to operate and no more.
- Using data solely for its intended purpose.
- Restricting access to data based on who needs to view it.
Consider your employees’ bank account numbers. You must retain this information while they work for your company to pay their wages. However, there is no legitimate reason to hold onto it when they quit.
“Once the purpose [of the collected data] is met, the data should be deleted or de-identified,” advised Harvey Jang, Cisco vice president and chief privacy officer.
Data minimization is essential because cybercriminals continually fine-tune their approaches. Even if you’ve done everything possible to protect your company from a data breach, one may still occur. With effective data minimization practices, the information they can access is reduced.
Jang says data minimization is essential to data protection, governance and data hygiene. “It helps mitigate against security breaches by reducing the data available to be exploited by either not collecting it in the first place or deleting it after it’s no longer needed,” Jang explained. “Hackers can’t steal what doesn’t exist.”
Robust
data management practices, including data management software, will help you centralize your data and assess what's essential and what can be destroyed.
How do you apply data minimization?
Data minimization requires a comprehensive implementation plan that includes four key principles.
1. Narrow data collection.
Focus your data-gathering techniques to ensure you only collect essential information. Once data is deemed necessary to collect and keep, controlling access to it is critical. For example, an admin professional may not need access to specific customer data, while a sales rep or customer service agent might.
Jang emphasized that clearly defined, strict access controls are necessary to protect confidential information. “Access rights should be limited to those who need to know,” Jang explained. However, assigning access rights often requires collecting additional personal and confidential employee data for authentication. “Businesses should minimize the data they use for authentication, collecting only what is necessary and proportionate,” Jang advised.
Multiple tools and services can help businesses define and control access to their data sets. For example, the best call center software allows businesses to restrict customer data by user type. As we explain in our GoTo Contact Center review, this platform allows companies to customize the data system administrators, supervisors and agents can see by role.
2. User verification and screening.
Many bulk data collection workflows operate under the assumption that the vast majority of collected data is usable and relevant. In reality, businesses often collect significant amounts of risky data. Data stored on company servers could be inaccurate or outdated, exposing the business to unnecessary risks.
Strong data minimization plans incorporate user verification and screening processes to weed out problematic data. For instance, a rideshare company with such tools in place could catch a criminal attempting to submit someone else’s personal details. [Read related article: What Is a Criminal Background Check?]
Data minimization plans also ensure that only verified, real users can access a platform. This screening, through tools like CAPTCHA checkboxes and puzzles, helps screen out bots.
“By verifying your user is human, and directly has interest in your organization, you can better tailor their experience with your products and services,” Hall pointed out. “This reduces the bad data and fake user info that would be collected otherwise, so you can now focus your resources on servicing your true customers.”
With these initial assessment procedures in place, organizations will gather only usable information from verified sources.
3. Progressive data management.
User data eventually becomes outdated, but many organizations don’t account for this. This results in databases full of unusable or incorrect information. This outdated data places a burden on IT infrastructure; plus, if it’s used for business data analytics, it will skew results.
“When data is no longer needed, it shifts from being an asset to a liability,” Jang cautioned. “There is very limited business benefit to over-retention, just increased cost and risk. Businesses should always consider the cost, benefit and ROI of their data retention practices.”
Data minimization plans that include progressive evaluation protocols avoid this issue, ensuring users keep data accurate and updated. This approach also simplifies database management for actionable reporting. In the long run, the business saves time and money; it also better mitigates the risk that comes with the growth of user data.
4. Strategic deletion.
All user information has a lifespan, especially in today’s fast-moving digital marketplace. Businesses must consistently purge stale data from their servers to maintain data value and reduce security risks. As a result, all data minimization plans should include strategic deletion protocols.
“The best way to deal with future stale data is to manage your file structure with your full data lifecycle in mind from day one,” Hall advised. “For a business, this would mean intentionally structuring your file system to reflect the ebbs and flows of your business’s accounts, opportunities or projects.”
Decisions on a business’s future direction should always include two things: identifying the new types of data a company needs and deleting outdated information that no longer serves the organization.
“Records management and information governance models (e.g., IGRM v.4) are useful in framing how to manage the data lifecycle from creation and collection to use, processing, transfers, sharing, retention and disposition,” Jang explained. “Security and data protection must be maintained throughout the lifecycle.”
Any time you store data, you are vulnerable to breaches, unverified data and more. There’s no way to eliminate those risks. However, companies that adopt sound data minimization strategies can streamline data collection, gather more valuable information and reduce risk.
Data management systems streamline
data complexity by automating the tedious tasks of unifying and reviewing critical information and consolidating data into insightful reports with contextualized visualizations.
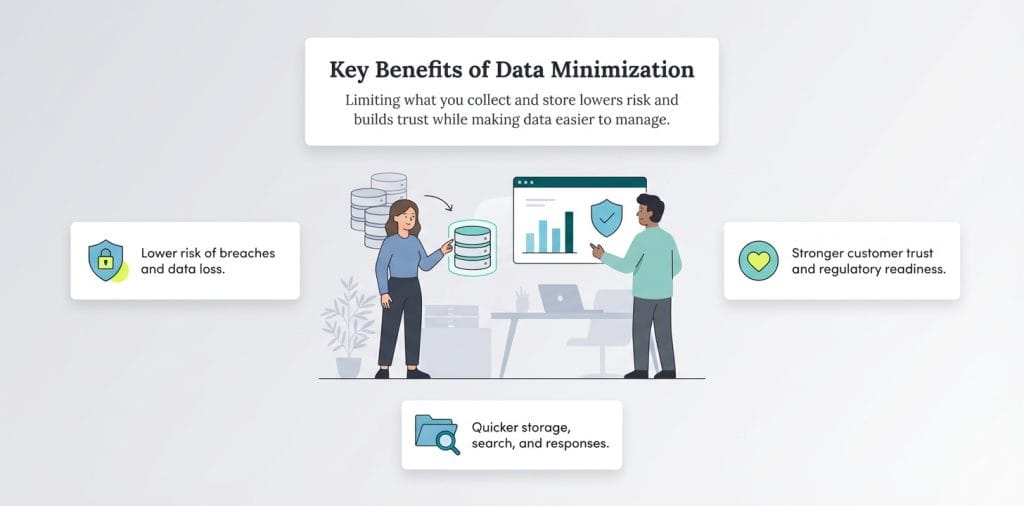
What are the benefits of data minimization?
Data minimization is a requirement for any business or organization that must comply with the European Union’s General Data Protection Regulation (GDPR). However, according to Jang, the benefits of data minimization go far beyond compliance. “Limiting the data you collect and process to only that which you need will improve operational efficiency, reduce risk and build trust — as a vendor, employer and data steward,” Jang said.
Consider the following benefits of data minimization:
- Reduced risk of data loss: Keeping fewer records decreases the likelihood of a data breach and its potentially devastating consequences. For example, in the U.S. health care sector, the average data breach in 2024 affected 300,000 records, according to the HIPAA Journal. Additionally, the global average cost of a data breach was $4.88 million in 2024, according to IBM’s Cost of a Data Breach report. By retaining only essential records, businesses can reduce the chances of a breach and minimize its impact if it occurs.
- More efficient data retrieval and storage: Data management is simpler when there is less of it. When disciplined minimization is practiced, knowledge workers can spend less time hunting through archives. Also, they can feel confident they’re retrieving the most current data.
- Faster responses to requests: It is easier to respond to requests when there is less stored data.
- Enhanced customer approval: Customers prefer to be asked for less personal data; they trust companies that provide assurances about what data is stored.
- Preparedness for future regulations: Companies enacting data minimization efforts now will be ahead of the game if regulations similar to GDPR are passed in the future.
Data minimization can maximize security and efficiency
Hall likens data minimization to cleaning out a messy closet. If organizations don’t employ data minimization, their “closet” becomes a jumbled mess of old and new clothes that’s nearly impossible to sift through. In this case, data minimization is donating or discarding old clothing to make it organized.
“A clean closet means anything you grab would be useful,” Hall explained. “The same is true for your minimized data. By eliminating junk or stale data, you can draw more insightful conclusions from the data you retained.”
Data minimization shouldn’t stop SMBs from embracing big data. However, it’s crucial to approach data management with the goal of protecting your business’s sensitive information from the start. “The longer you wait to implement data minimization processes, the harder it will be to build a culture of data governance in your organization,” Hall warned.
Jeremy Bender contributed to this article.