Below, we break down 10 ways big data is transforming business and share best practices to help you use it wisely in your own company.
How big data is changing business
Here are 10 ways big data is changing business.
1. Better business intelligence (BI)
Business intelligence combines data tools and data analytics to help companies make smarter decisions. It goes hand in hand with big data because BI platforms pull insights from large, complex data sets. The global BI market is projected to reach about $108 billion by 2035, highlighting how essential these tools have become in modern business strategy.
Today’s BI platforms are far more advanced than the reporting tools of the past. Cloud-based systems and real-time analytics allow businesses to monitor performance instantly and react quickly to market changes or shifts in customer behavior. Many solutions also include natural language processing, which lets non-technical users ask questions in plain English and generate reports without needing help from a data specialist.
Almost any business that generates data — which is nearly all of them — can benefit from business intelligence. Whether it’s tracking sales trends, reviewing customer activity or identifying operational bottlenecks, modern BI tools make it easier for teams to turn raw data into actionable insights.
2. More targeted marketing
Big data has transformed how companies deliver personalized marketing. Before big data, businesses relied mostly on past sales to understand their customers. Today, companies can track and interpret billions of customer interactions across channels — from website activity and mobile behavior to email engagement and past purchases. And customers now expect brands to use that information to deliver more relevant experiences. McKinsey reports that 71 percent of consumers expect personalized experiences, and 76 percent feel frustrated when they don’t get them.
With big data, companies can capture even the smallest customer actions and use them to create campaigns tailored to each person’s interests and behavior. This includes personalized offers through email, websites, streaming platforms and digital ads. Advanced AI and predictive analytics can now simulate and anticipate customer behaviors with an average normalized accuracy of 85 percent, making it possible to deliver proactive recommendations and prevent churn before it happens.
Imagine how your business could benefit if you knew exactly which products customers needed and how to tailor your message to them. That’s the level of precision big data brings to modern marketing.
3. Proactive customer service
Big data is reshaping customer service by giving companies a way to understand what customers need before they speak up. That proactive approach can set a business apart, especially when great service is a key competitive edge.
Modern customer service platforms now use sentiment analysis and behavioral prediction models to spot at-risk customers and potential issues early. For example, some telecommunications companies analyze network performance and user behavior to predict service disruptions, then offer solutions or compensation before a customer even notices a problem.
AI is playing a major role in this shift. AI chatbots and virtual assistants trained on large datasets can resolve routine questions quickly and hand off complex cases to human agents with full context of the customer’s history and likely needs. And the technology is improving quickly. According to Gartner, AI chatbots will be able to resolve 80 percent of common customer service interactions by 2029, reducing operational costs by 30 percent.
Proactive customer service doesn’t just solve problems faster — it builds trust. When customers feel understood and supported without having to ask, it strengthens loyalty in a way reactive service can’t.
4. Customer-responsive products
Big data isn’t just improving customer service — it’s also transforming how companies design and refine their products. Instead of guessing what customers want or waiting for feedback after launch, businesses can now use real-time data to understand how people actually use their products and what they expect next.
Many companies rely on digital twins and simulation models powered by live data to test thousands of product variations before anything is built. This kind of virtual prototyping can cut development costs and reduce time-to-market, giving teams a faster way to experiment and improve product quality.
IoT-enabled products make this even more powerful. Because connected devices can share usage data directly with manufacturers, they create an ongoing feedback loop that shapes new features, improvements and design updates. That information helps companies build products that feel more natural and better suited to how customers truly use them.
Big data makes product development less of a guessing game and more of an ongoing conversation with your customers, even if they never say a word.
5. Rise of the chief data officer (CDO) and data departments
Big data isn’t just changing how companies interact with customers; it’s reshaping how they operate internally. In the 1980s and 1990s, IT departments powered major productivity gains and ushered in the rise of the chief information officer. Today, data is driving the next evolution. Many companies are building dedicated data departments separate from IT and appointing chief data officers who report directly to the CEO.
These teams often include data engineers, data scientists, machine learning experts and data governance specialists. Together, they create an ecosystem focused on extracting insights, maintaining data integrity and embedding analytics into everyday decision-making.
According to the 2025 AI & Data Leadership Executive Benchmark Survey, more than
84 percent of companies now employ a CDO or chief data and analytics officer, a major leap from just 12 percent in 2012.
6. Improvements in operational efficiency
Operational efficiency has always been a priority for industrial engineers, and big data is now giving them the insight they need to streamline processes at a level that wasn’t possible before. Modern facilities generate massive amounts of information about how products are made and how equipment performs, and engineers can analyze that data to pinpoint inefficiencies and uncover new opportunities for improvement.
Many manufacturers now rely on thousands of sensors that produce terabytes of data a day, enabling predictive maintenance and real-time monitoring. According to McKinsey, predictive maintenance can lower instances of machine downtime by 30 to 50 percent and even boost machine life by 20 to 40 percent. It can also cut maintenance costs by 25 to 30 percent, according to the Department of Energy.
Big data also works well with long-standing operational frameworks like the theory of constraints. Data makes it easier to identify bottlenecks and validate whether a particular constraint is truly the limiting factor. Once the most significant constraint is removed, companies can see major gains in performance and throughput. Machine learning models can also support real-time process optimization, helping increase overall equipment effectiveness by 15 to 20 percent in manufacturing environments.
Using
big data in human resources can also help streamline workforce management and improve how companies schedule, allocate and support their teams.
7. Reduced costs
Big data is giving companies new ways to cut business costs, especially when paired with business intelligence tools. By analyzing historical patterns and using machine learning to forecast future trends, businesses can make smarter decisions about production, inventory and budgeting. Advanced forecasting models can now predict demand with up to 98 percent accuracy, allowing companies to optimize their inventory and reduce carrying costs by 20 to 30 percent.
Inventory is a perfect example. Holding too much stock ties up capital, takes up storage space and increases the risk of waste or obsolescence. Big data helps businesses anticipate when customers will buy and when production should ramp up, minimizing the cost of keeping excess inventory on hand.
Pricing is another area where big data drives savings. Dynamic pricing algorithms that analyze competitor behavior, demand patterns and outside factors in real time can increase profit margins by 2 to 5 percent while still keeping prices competitive.
When businesses can see what’s coming — even a few weeks ahead — they can plan more efficiently, reduce waste and redirect resources to higher-value opportunities.
8. Better fraud detection
Big data is helping companies detect fraud faster and more accurately than ever before. In financial services and insurance, machine learning models trained on billions of transactions can flag suspicious activity in milliseconds. Some systems now reach accuracy rates above 99 percent and can reduce false positives by up to 60 percent (according to one case study), making fraud detection both stronger and more efficient.
Banks and payment processors also rely on big data to catch credit card fraud — sometimes even before the customer realizes their card has been compromised. Advanced techniques like graph analytics and network analysis can uncover complex fraud rings and money laundering schemes by identifying unusual patterns and connections across millions of accounts.
Big data gives fraud teams a level of visibility they couldn’t get from manual reviews or basic rules alone, helping businesses protect customers, reduce losses and respond to threats in real time.
9. More robust cybersecurity
Big data is also strengthening cybersecurity and risk management by helping companies spot threats earlier and react faster. Security information and event management (SIEM) systems now analyze billions of events each day, using behavioral analytics and machine learning to detect zero-day attacks and advanced data breach threats that traditional signature-based tools often miss.
Today’s security teams aren’t just analyzing logs from computers and mobile devices. They’re pulling data from networks, sensors, cloud platforms and connected devices to uncover patterns that signal unusual activity. Extended detection and response (XDR) platforms bring all of this information together. By consolidating data across endpoints, networks and cloud workloads, XDR gives security teams a unified view of their environment and helps them detect and respond to threats up to 60 percent faster than traditional approaches.
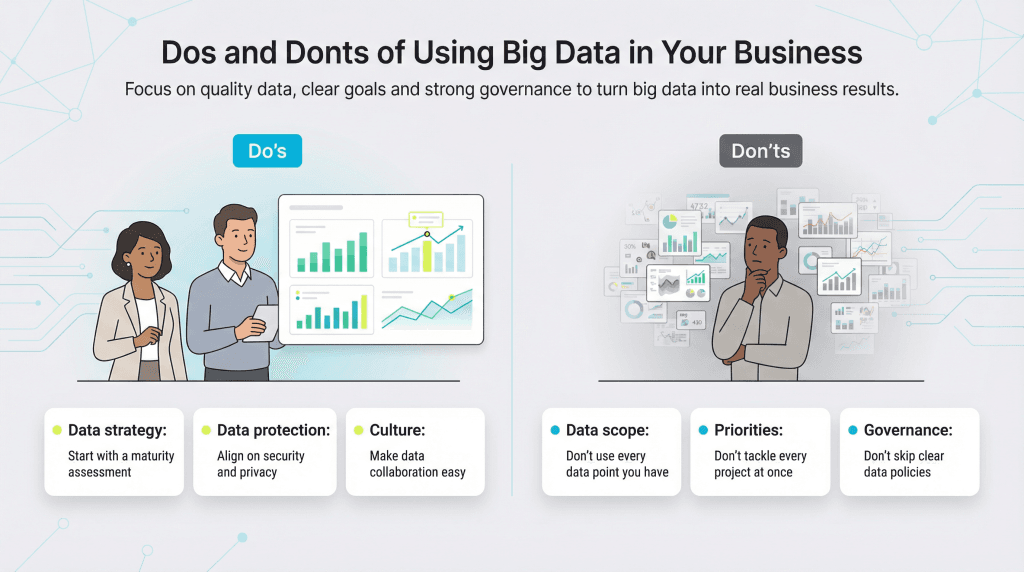
Before launching big data initiatives, make sure your organization is ready for a more collaborative, data-driven approach.
Company culture is often one of the biggest obstacles to adopting analytics effectively.
10. Supply-chain risk mitigation
Big data is giving companies the ability to identify and respond to supply-chain risks far earlier than before. AI-powered supply chain control towers pull in real-time data from suppliers, carriers, ports, inventory systems and external factors like weather or geopolitical events to provide full end-to-end visibility. With this level of insight, businesses can adjust production plans, reroute shipments or switch suppliers before small issues turn into major disruptions.
Big data also plays a major role in improving delivery and logistics. Route-optimization tools now analyze traffic conditions, weather patterns and delivery constraints to recommend the most efficient paths for drivers. These tools help businesses coordinate schedules, increase delivery reliability and track items with far greater precision.