As remote and hybrid work arrangements grow in popularity, information technology (IT) teams must be able to access desktops remotely. This way, they can view or change files, fix technical issues, or configure settings at any time. However, this convenience comes with an increased risk of cyber threats and security issues. Ensuring secure remote access is essential to protect your business from data breaches and other security vulnerabilities.
Despite talk of return-to-office mandates,
remote work plans aren't going anywhere. According to an
Owl Labs report, 27 percent of U.S. employees currently work in a hybrid setup, while 11 percent are fully remote.
What is secure remote access?
Secure remote access is technology often used by IT personnel to help colleagues with tech problems from afar. It’s also helpful for workers who must log in to a secure device connected to their company server in the office while working from a personal device at home. Another use is for managers who want to monitor what their employees are accessing on their company devices.
If you grant team members access to company devices or systems, implementing security measures to prevent unauthorized access to your programs and data is critical. Secure remote access systems involve the best remote PC access software and other strategies designed to help protect computers and networks from falling into the wrong hands.
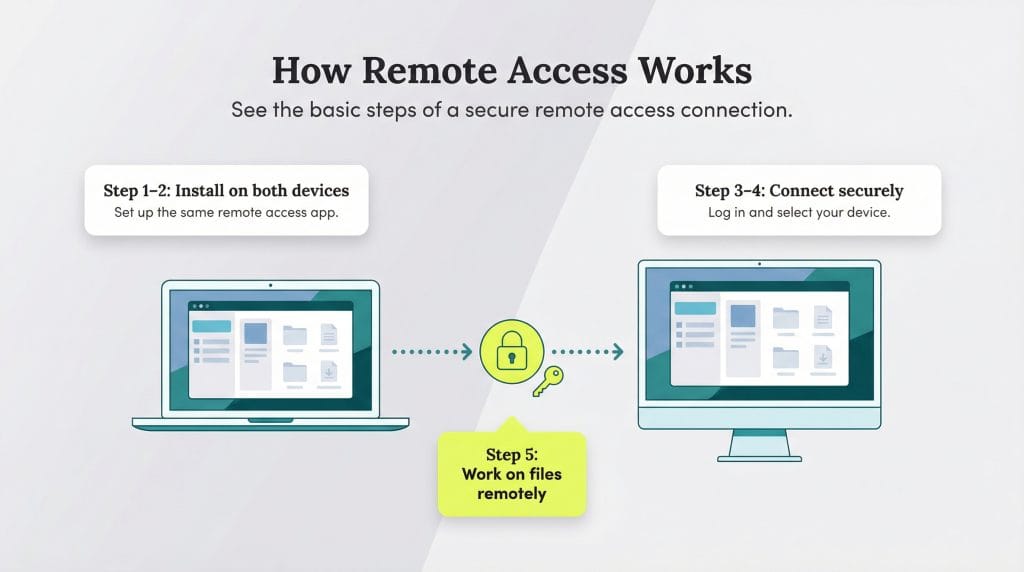
How does remote access work?
- Install remote access software on the device you're using.
- Install the same application on the device you need to access remotely.
- Power on both devices.
- Log in to the software and select the device you want to access.
- The software will mirror the remote device's screen, and the authorized user can access, share and download that device's files.
Sammy Basu, founder and CEO of CarefulSecurity.com, emphasized the importance of authentication and authorization in a secure remote access system. “Authentication validates [that] you are who you say [you] are, which … provides nonrepudiation, which is you cannot deny and say it was someone else because we have irrefutable evidence,” Basu explained. “Once you are allowed access after validating your identity, you should only have access to the systems and data you have access to. Nothing more, nothing less. It is based on the principle of least privilege, the foundational block of cybersecurity.”
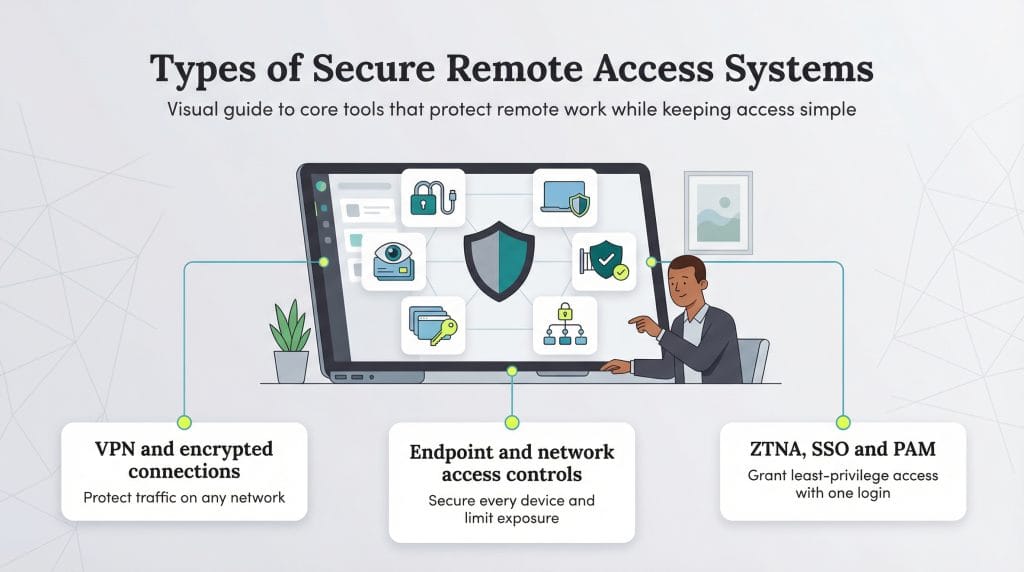
What are the different types of secure remote access systems?
Several options exist for securely accessing a device or program from a different location. Some solutions can be used concurrently, depending on the required access level and security.
“Go for solutions that are simple for your IT department and employees to work with [and can] easily adapt to their distributed teams’ needs,” advised Sahin Boydas, entrepreneur and founder of RemoteTeam (since acquired by Gusto). “The work environment is changing … and your company needs will also keep changing. A solution that can accommodate your team’s workflow and changing environment is the best option.”
These are some of the most common types of secure remote PC access:
- Virtual private network (VPN): A VPN adds a layer of security for any device working remotely from its home system. It allows secure internet access by routing connections through an encrypted server. Users can then work over any home or public Wi-Fi network for their sensitive business needs without restrictions or fear of a breach.
- Endpoint security: An endpoint security system secures a company’s various devices on a network. These devices can include mobile devices, laptops, desktops and servers. Typically, top antivirus software and firewalls are installed on each device to help keep data secure.
- Zero-trust network access (ZTNA): This type of system allows secure remote access to applications and services based on a company’s policies. A ZTNA system defaults to denying access, unlike a VPN, which generally grants users open access with the proper credentials. The type of data, systems and access level a user has is determined by the company’s system setup. Businesses can implement their policies based on device location or type, allowing some organizations to limit access on unfamiliar networks.
- Network access control: Network access control is typically determined by an organization’s managers or the head of the user’s department. It allows them to restrict access to outside users and users within the organization who do not need it.
- Single sign-on (SSO): SSO technology is a user authentication process that grants the user access to multiple devices through a single set of credentials. The software allows users to log in to their computer, email, mobile device, and any other system or device with the same credentials. SSO lets users log in quickly while allowing the organization to manage user authentication and access.
- Privileged access management (PAM): PAM is a set of tools managers use to secure and monitor access to sensitive system data by tracking user activity across various accounts. PAM helps ensure security by allowing administrators to monitor user access and detect any unusual behavior.
Raviraj Hegde, SVP of Growth and Marketing at DonorBox, explained that remote access security strategies help protect sensitive data and operational continuity. “Major components of a comprehensive system include encrypted connections, such as through VPNs, endpoint security to protect devices and ZTNA that authenticates users to grant access at every touchpoint,” Hegde noted. “These elements all work together to minimize vulnerabilities while maintaining frictionless access for employees.”
Ensure your secure remote access measures help maintain a
strong company culture — not weaken it. Communication and team-wide access are critical to maintaining connections.
Why is secure remote access important?
Hegde stressed the importance of secure remote access for any organization with remote work components. “Securing remote access is no longer optional; it’s a strategic imperative for any forward-looking business,” said Hegde.
When employers take appropriate security measures to protect their business data in a remote work environment, they gain the following advantages.
1. Secure remote access enables safe remote work.
Secure remote access solutions grant authorized users access to your company network on any compatible device. Employees have seamless access to all necessary data and files, and the organization’s data stays secure.
Additionally, IT and engineering experts can troubleshoot users’ problems remotely. Whenever a technical issue arises, a specialized worker can access the user’s device remotely and help them find a solution quickly and efficiently.
2. Secure remote access ensures safe internet browsing.
For many modern companies, much of their employees’ daily workflow takes place on the internet. A secure remote access system protects your employees from web-based perils. Such dangers include phishing threats, ransomware attacks and malware while they’re logged in to your company’s network. Without protection, these cyber incidents can lead to unauthorized access to and use of both the company’s business data and the employee’s personal data.
3. Secure remote access protects multiple endpoints.
Today’s employees often use multiple devices to carry out work tasks. They may answer emails on a smartphone, input data on their tablets and log in to video meetings on their laptops. Each of these devices — known as endpoints — represents a potential security risk if not properly protected.
“Securing remote access is important because more and more employees are deciding to work remotely, and the protection of traditional corporate perimeter[s] no longer exists,” Basu explained. A secure remote access solution can protect all devices connected to your company’s network and systems. This practice ensures that sensitive information remains safe, regardless of where or how employees log in.
4. Secure remote access increases employee security awareness.
Any organization’s cybersecurity plan should include employee training on cybersecurity best practices and how their actions can affect the safety of company and customer data. Employee awareness is even more critical for companies with a remote work component.
Because secure remote access solutions require employees to follow security protocols by design, they inherently educate team members on safe digital practices. “Increased employee awareness is important, as we still need to manage the security of our individual devices both physically and with the awareness that we may introduce an inadvertent risk when we click on a malicious link or download unauthorized software,” Basu explained.
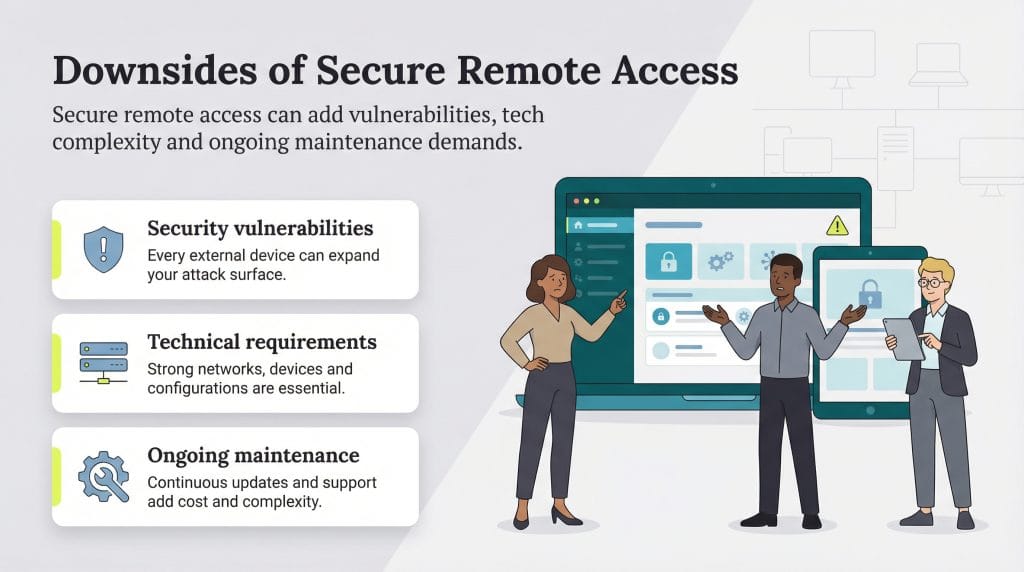
What are the downsides of secure remote access?
Secure remote access — or remote access that isn’t secure enough — can also bring several challenges to an organization, including the following downsides:
1. Secure remote access brings potential security vulnerabilities.
When you’re setting up a secure remote access system, the word “secure” is key. Without careful implementation and adherence to best practices, introducing a new system can open the door to security risks with each external device that connects to a company’s system.
By design, secure remote access systems feature data encryption, activity logs to monitor employee use and multiple permission levels. Still, ensuring access is granted only to authorized users can be challenging.
2. Secure remote access has technical requirements.
Successful remote access software implementation requires a robust technical infrastructure; the setup includes a secure and reliable internet connection, such as business broadband with sufficient internet speeds. Without an adequate tech setup, your employees can’t do their jobs effectively.
“While effective, secure remote access systems require a great deal of technical infrastructure and maintenance,” Hegde cautioned. “Poor configurations open up weaknesses in the systems, updates are continuously needed against evolving cyber threats, and, quite often, there is an operational challenge between comfort for the user and security.”
Additionally, solution providers may have other technical requirements — such as specific host computer specifications — that businesses must fulfill to implement the technology.
3. Secure remote access requires ongoing maintenance.
Remote access systems require regular upkeep to address issues such as system failures or necessary updates. This means businesses must have an IT professional or a technically skilled employee on standby to resolve system issues — remotely or in person, depending on the problem — as they arise.
In addition to the operational and staffing costs associated with software maintenance, system disruptions — such as failures caused by power loss — can impact daily workflows and lead to productivity losses.
Amanda Clark contributed to this article.