Remote access software connects work-from-home employees to company networks, enabling remote file access, printing, communication and more. It also gives information technology (IT) professionals direct control to address technical problems remotely. While these capabilities are essential for businesses with remote work plans, companies must ensure their access solutions implement robust security measures to protect business and customer data. We’ll explain the risks of remote access and share tips for remote PC access safety and security.
Potential remote access risks
Business and personal computers typically store sensitive data. When connected to the internet, anyone with the appropriate login credentials can access this data, potentially increasing productivity and convenience. However, Jon Heimerl, a security strategist with 40 years of experience across nearly half of the Fortune 100, cautioned that this connectivity also brings risks of cyberattacks, data breaches and other security threats.
“Remote access typically means the remote user can do pretty much everything you can do on your PC and probably more depending on how authorizations are defined,” Heimerl explained. “The remote user can see or copy any data on your system, can monitor any passwords you enter, can install new software (including malware) or take similar actions to obtain access to information, your PC or other PCs on your local network.” When malicious intent accompanies such open access, company and customer data is at risk.
Editor’s note: Looking for employee monitoring software for your business? Complete the questionnaire below to have our vendor partners contact you with free information.
Consider the following specific cyberrisk areas you face when allowing remote PC access.
1. Authentication
When you access PCs remotely as part of your daily work, you might become complacent about security over time. However, the bad actors seeking access to your sensitive data rely on a lax attitude.
Be cautious when allowing access to your device or system. Hackers can pose as co-workers, acquaintances or even family members, using business scams and phishing emails to trick you into granting access. For example, a cybercriminal could claim to be from your company’s IT department and tell you they must perform remote repairs or updates. When you turn over your login credentials, they’ve won.
Heimerl emphasized the importance of adhering to strict authentication protocols when seeking and granting remote access to a computer. “The single most important step in this process is making sure that the person who is granted remote access to your PC is actually authorized to do so,” Heimerl warned. “One way of helping ensure this is that the PC user should always be the one initiating a remote access request. You should never accept a remote access request that comes from an unsolicited person or comes from an inbound phone call.”
Always know and trust the person to whom you're giving remote access. Treat your computer like your home — you wouldn't give your keys to just anyone.
2. Network access
The risk of a data breach increases when remote access software is used to log into a business’s network. Without proper protections, an outside entity could gain access to all computers connected to the network, leaving company assets and sensitive customer data vulnerable.
More secure networks are segmented into isolated sections, restricting the data and apps hackers can access to the specific section they manage to infiltrate. This setup limits the harm they can inflict on your business.
3. User error
Human error is often at the root of data breaches. Employees without proper cybersecurity training can inadvertently invite cybercriminals into a network, risking the company’s data, finances and reputation.
Even worse, rogue employees may deliberately create risks and problems by abusing their access to sensitive data. For example, they may seek to sell trade secrets or leak confidential data. Without robust role-based access controls and monitoring measures, these inside threats can exploit remote access software to cause significant damage.
Heimerl emphasized that properly configured remote access software should not compromise standard security practices or user behavior. “In general, the existence of remote PC access software should not substantially change a user’s behavior,” Heimerl noted. “The remote access software should be configured to not allow access unless the user explicitly allows it, so they should be able to use their PC and function as if they had no such software.”
Even the most security-conscious businesses can be victims of a cyberattack. Consider taking out
cyber insurance to cover many of the costs incurred by a successful breach.
4. Too many devices
Every remote access device must be vetted and secured. When too many devices overwhelm your IT infrastructure, the likelihood of mistakes and oversight increases. One of the greatest risks occurs when individuals use unvetted devices for remote access, effectively bypassing your existing security measures.
One of the best ways to vet devices is to require every device to undergo a security audit before giving it access credentials. Implementing measures like MAC address filtering and internet protocol profiling adds automated security layers that prevent unvetted devices from gaining access to your network.
Tips for remote PC access safety and security
While the best remote PC access software incorporates robust defenses, including permissions and access controls, it is essential to use these solutions correctly and integrate them into a comprehensive cybersecurity plan.
“In the new age of work, the ability to access business-critical applications, such as Salesforce, Zoom and Slack, and data from any location has drastically increased an organization’s risk of breach,” cautioned Anupam Upadhyaya, vice president of Prisma SASE at Palo Alto Networks. “Organizations must ensure consistent protection and user experience for their entire workforce, regardless of where they reside.” Consider the following tips to help ensure safe and secure remote PC access.
1. Practice strong digital security measures.
Weak passwords for online accounts pose a significant security risk. Since most remote access software requires users to sign in to start a new session, ensure you and your team follow strong password practices to prevent unauthorized access.
Whenever possible, implement multifactor authentication (MFA). MFA requires anyone logging into your account to provide another verification form, such as a code sent to their phone or email address. Single sign-on solutions, such as platforms like Okta or OneLogin, are another great option that enhances login security by streamlining and securing authentication across varied platforms.
2. Consider an account lockout limit.
If you’re a software administrator for your company, you can set an account lockout policy. This practice prevents access either permanently or for a predetermined length of time if someone enters the wrong password a specific number of times.
3. Use a firewall.
Remote access software creates a virtual connection between two computers. If an intruder intercepts that connection, they could quickly gain access to one or both machines. Firewalls constantly check the digital traffic in and out of a network, blocking any connection that doesn’t meet security parameters.
4. Keep your software up to date.
Software updates may seem inconvenient, but ignoring vendor warnings and reminders can leave your devices vulnerable. Many updates are designed to address and patch security vulnerabilities in a program’s code. Without these fixes, intruders could exploit weaknesses to access your device or it could become susceptible to malware and viruses. Failing to update your software also means missing out on potential performance improvements or valuable new features.
5. Set remote access limits.
If your company relies on multiple people gaining remote access to your IT systems, limit the number of people with that capability. Administrators can also adjust settings so only a trusted device can log in.
6. Consider a VPN.
Heimerl recommended using a virtual private network (VPN) as a security measure. “Remote sessions should be conducted across a VPN or a network protected by some other means of encryption,” Heimerl advised.
Though this option will add another cost to your remote access budget, VPNs offer one of the most secure ways of allowing access to your IT system. A VPN provides a much more secure internet connection. Using a VPN in conjunction with a remote access solution enables your employees to safely connect to a network or device without fear of detection by someone else trying to gain access.
7. Avoid public Wi-Fi.
If you’re using a remote access solution in public, never connect to a public Wi-Fi hotspot. Though tempting, public networks are inherently insecure and are prime locations for tech-savvy troublemakers to gain access to your data. If secure business Wi-Fi isn’t an option and you must connect to public Wi-Fi for remote access, always use a VPN for an extra layer of protection.
8. Limit actions during remote access.
Heimerl advised users to limit their actions to only required functions and tasks during a remote access session.
“For instance, if [dealing with] a technical IT support problem, the local PC user should focus on those tasks required to support troubleshooting and resolution of their issue that generated the remote session,” Heimerl explained. “If access to email or specific applications or databases with sensitive information is not relevant to the issue, the user should close that email, database or other application to limit any potential exposure.”
Additionally, according to Heimerl, a good rule of thumb during remote access sessions is to never enter a password unless that password or access is explicitly required for the problem at hand.
9. Implement a zero-trust security approach.
By implementing a zero-trust security approach, businesses can enhance their overall security and the security of any remote connections further. This framework requires ongoing validation and strict access controls for every digital interaction to minimize potential threats.
“This means organizations can eliminate implicit trust and continuously validate and inspect every digital interaction within their network, securing all connections to and from applications, users, data and devices,” Upadhyaya explained. “And this protection must extend throughout the entire network so that no matter where a user resides, they will benefit from the same level of protection.”
Secure remote access best practices help prevent unauthorized intrusions into devices and networks while ensuring safe internet browsing, protected endpoints and increased employee security awareness.
Choosing the right remote access software solution
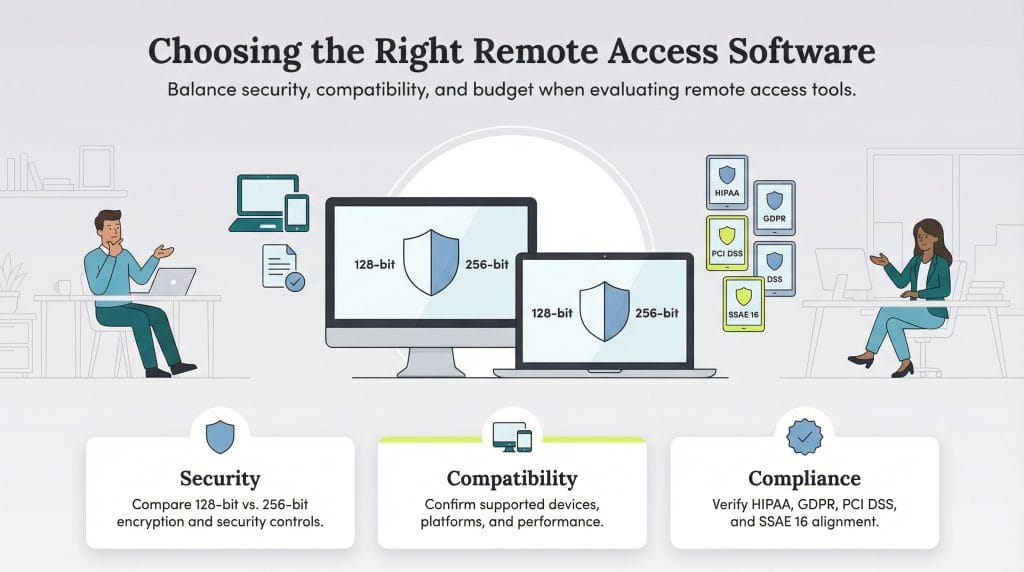
Remote access solutions come with varying features and functionality. You’ll need to evaluate your business’s needs and budget and ensure all devices that must connect are compatible with your chosen solution.
When considering remote access software features, look for tools with robust reporting and chat functionality to enhance workforce collaboration and operational efficiency.
However, any potential solution’s security measures will be your primary concern. While the industry standard is 128-bit encryption, many companies prefer the more secure 256-bit AES method. Most remote PC access tools will specify the strength of the encryption they use between machines. 256-bit encryption provides stronger protection than 128-bit encryption, making it significantly more resistant to brute-force attacks. However, this increased security often comes with speed and efficiency tradeoffs.
Additionally, compliance with essential legal guidelines, such as the Health Insurance Portability and Accountability Act, General Data Protection Regulation, Payment Card Industry Data Security Standard and Statement on Standards for Attestation Engagements No. 16, will be a critical consideration when evaluating solutions.
Jeremy Bender contributed to this article.