Keeping your data, customers, staff and assets safe is essential. Every time a business experiences an intrusion, theft or damage, resolving the issue costs money. If these incidents happen repeatedly, they can put the company’s future at risk. Even so, many entrepreneurs struggle to find the time and resources to give business security the attention it deserves.
The financial stakes are high. According to IBM’s 2025 Cost of a Data Breach Report, the global average cost of a data breach is $4.44 million, with costs still varying widely by industry and region. For many small businesses, a single breach can be devastating. That’s why understanding the importance of security and putting the right measures in place is worth the time, cost and effort.
How security supports business growth
Business security plays a bigger role in growth than many owners expect. It helps build customer trust, reduces the risk of costly data breaches and keeps your business aligned with evolving regulations. It also helps keep things running when something goes wrong, limiting disruptions from cyberattacks and other incidents that can slow you down.
Enhanced customer trust
Security plays a direct role in how customers feel about and interact with your business. In fact, research from Cisco’s 2026 Data Privacy Benchmark Study found that 95 percent of organizations say their privacy investments help strengthen customer loyalty and trust.
When customers feel confident their information is protected, they’re more likely to complete purchases, return in the future and recommend your business to others. But trust is hard to rebuild once it’s lost. Even a single incident can create hesitation, making it more difficult to retain customers and convert new ones.
Reducing costs and protecting your bottom line
Security investments can have a measurable impact on your bottom line, especially when something goes wrong. According to IBM’s 2025 Cost of a Data Breach Report (cited above), organizations that use security-related AI and automation technologies extensively reduce data breach costs by an average of $1.9 million compared to those that don’t.
Much of that difference comes down to timing. Teams using these tools tend to identify and contain breaches faster, limiting how far an incident spreads and how expensive it becomes. That kind of cost control can free up capital that would otherwise go toward damage control, allowing businesses to reinvest in growth instead.
Regulatory compliance and market access
Compliance with industry regulations like the General Data Protection Regulation (GDPR), SOX and PCI DSS plays a direct role in where and how your business can operate. In many cases, it determines whether you can enter certain markets, work with specific partners or process payments at all.
For example, PCI DSS 4.0, which has been fully enforced since 2025, is required for any business that accepts credit card payments. Falling out of compliance can lead to fines, but it can also mean losing the ability to process payments — an immediate hit to revenue and day-to-day operations.
Operational continuity and productivity
Security plays a key role in keeping your business running when something goes wrong. IBM’s 2025 research found that it takes organizations an average of 241 days to identify and contain a data breach. That’s months of potential disruption, from system downtime to delayed operations and lost productivity.
Strong security measures can shorten that timeline. Teams with the right tools in place are able to detect and respond to incidents faster, limiting how far a breach spreads and reducing the impact on day-to-day operations. That helps businesses maintain momentum while others are still dealing with recovery.
Cybersecurity: Defending your digital assets
With most devices now connected to business internet and business Wi-Fi, attackers don’t need physical access to cause damage. Sensitive data, intellectual property and even day-to-day operations can all be compromised remotely.
At the same time, the threat landscape continues to shift. According to Verizon’s 2025 Data Breach Investigations Report, the human element plays a role in about 60 percent of breaches, while stolen or compromised credentials remain one of the most common attack methods. The share of breaches involving third parties has also increased significantly, highlighting how risks often extend beyond your own systems.
No business is too small to be a target. That’s why effective cybersecurity isn’t a single tool or policy; it’s a set of practices that work together to reduce risk and keep operations running. The following areas are a good place to start.
Secure your network and manage connected devices.
Any device connected to your IT network can become a point of vulnerability. To stay on top of potential risks, keep an up-to-date list of devices that can connect to your network. Include everything that connects wirelessly, from security cameras to shared printers. If a device isn’t recognized, block it from connecting.
You may also want to follow the National Institute of Standards and Technology Cybersecurity Framework 2.0. It offers practical guidance for organizations of all sizes and adds a “Govern” function alongside Identify, Protect, Detect, Respond and Recover, emphasizing that cybersecurity is an ongoing business responsibility, not just an IT task.
Avoid risky physical media.
While their use has declined, some employees still rely on CD-ROMs, USB drives and other portable media. These devices are easy to lose, easy to share and difficult to secure, all of which increase the risk of data exposure.
The risk grows when devices are used across personal and work environments. A file downloaded at home, for example, could carry malware that spreads to your business network when the device is plugged in at work.
Cloud-based storage services and file-sharing tools offer a more secure alternative. Platforms like Dropbox or Google Drive include access controls, version history and encryption, helping reduce risk while keeping collaboration simple.
Train employees to recognize and report threats.
Employees are often the entry point for security incidents, usually without realizing it. A common example is clicking on a link in a phishing email, which can introduce malware or expose sensitive information.
Training can reduce that risk. According to IBM’s 2025 report, phishing is the most common initial attack vector, responsible for about 16 percent of breaches. That makes employee awareness one of the most practical ways to reduce security risk.
“Start with regular training sessions that are simple and engaging, using real-life examples to illustrate potential threats,” advised Adhiran Thirmal, senior technical architect (product security) at GitLab.
Employees should also feel comfortable reporting suspicious activity. “Encourage a culture where employees feel comfortable reporting suspicious activities without fear of reprimand,” Thirmal said. “Recognize and reward proactive behavior, and make sure that leadership consistently emphasizes the importance of cybersecurity in everyday operations.”
Employee training is one of the most effective ways to reduce security risk. Build a program that reinforces good habits and makes it easy for employees to flag potential issues early.
Detect and respond to threats faster.
Cybercriminals tend to look for easy entry points. The harder your systems are to access and monitor, the less likely they are to become a target.
At a minimum, consider using a modern firewall to monitor and filter network traffic. These tools can help detect suspicious activity early and block potential threats before they spread.
More advanced tools take that a step further. Extended Detection and Response (XDR) solutions and other AI-driven security platforms help organizations identify and respond to threats across systems in real time.
According to IBM’s 2025 report, organizations that use security AI and automation extensively identify and contain breaches an average of 80 days faster than those that don’t. That difference often determines whether an incident is contained quickly or turns into a massive operational disruption.
Secure remote connections and public Wi-Fi access.
Connections outside the office are often less secure, especially on public Wi-Fi networks. When possible, employees should avoid using public Wi-Fi altogether and rely on cellular connections instead.
One common risk is spoofed access points. Cybercriminals can create fake networks using a venue’s name to trick users into connecting. Once connected, any data sent or received may be exposed.
If employees need to use public Wi-Fi, require them to connect through a VPN. The best VPN services encrypt data in transit, which helps protect sensitive information even if the network itself isn’t secure.
“Encryption and VPNs are vital for keeping data secure, especially when it’s in transit or accessed remotely,” Thirmal said. “VPNs add a layer of security by encrypting data and verifying the identity of users, even on public or unsecured networks.”
To help ensure
e-commerce website security, use a platform with built-in protections, implement SSL certificates and require VPN access for remote connections.
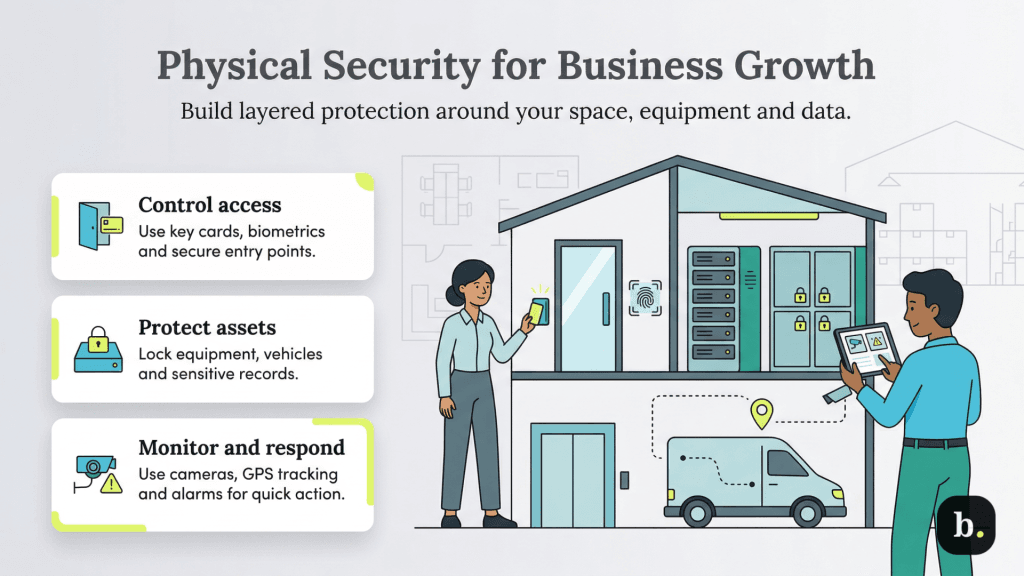
Physical security: Protecting your foundation for growth
Physical security plays just as important a role as cybersecurity in protecting your business. Safeguarding your location, equipment and other assets helps prevent losses that can disrupt operations and limit your ability to grow.
“I’ve seen how physical security directly supports the growth of businesses,” said Eugene Klimaszewski, CEO of electronic security firm Mammoth Security. “Your assets are better protected, and your losses are lower, meaning you have more money to invest in growth.”
The following best practices can help strengthen your physical security and support long-term stability.
Track and monitor physical assets.
Keeping track of your physical assets is a key part of preventing loss and maintaining control over day-to-day operations. GPS fleet management systems typically include trackers that can be attached to vehicles and high-value equipment, giving you visibility into where assets are and how they’re being used.
Many systems provide near-real-time location data, making it easier to spot unusual movement or unauthorized use. That visibility can help you respond quickly if something goes missing and reduce the risk of longer disruptions.
Secure and store valuable equipment properly.
Devices like desktop computers, tablets and projectors are easy to move and just as easy to steal if they aren’t secured properly. Even when the hardware itself isn’t especially valuable, the data stored on those devices can be.
In some cases, devices may still be logged in or connected to your network, which increases the risk if they’re lost or stolen. That can expose sensitive information and create a path back into your systems.
Setting up a designated place to store equipment (like a locked room or cabinet) gives employees a clear, consistent way to secure devices when they’re not in use. It’s a simple step that helps protect both the equipment itself and the data stored on it.
Use professional security services to deter theft.
On-site security guards remain one of the most visible and effective ways to deter theft. They can monitor who enters and exits your premises, helping manage access for customers, employees and visitors. Guards are just as useful in large warehouses as they are in retail environments, where inventory may be more exposed.
If around-the-clock coverage isn’t practical, mobile patrol services offer a flexible alternative. Patrols can check your property after hours and respond quickly if an alarm is triggered or cameras detect unusual activity.
In many cases, patrol teams can also serve as keyholders, allowing them to grant access to law enforcement if there’s a break-in. That can speed up response times and reduce delays when an incident occurs.
Strengthen access control at entry points.
Standard locks can only do so much. For many businesses, upgrading access control is one of the first steps toward improving physical security.
Modern access control systems let you manage who can enter your space and when. They can also double as visitor management tools, helping you track activity across your location.
Klimaszewski recommends choosing a system that fits your size and security needs. “For small to medium businesses, key card systems are a smart pick, costing between $1,000 to $3,000 per door,” he said. These systems use RFID-enabled cards or fobs that unlock doors when held up to a reader.
Larger facilities or higher-risk environments may require more advanced options, like biometric authentication tools. “For those overseeing larger facilities or requiring enhanced security measures, investing in biometric systems such as fingerprint or retinal scans is advisable, despite the potential cost exceeding $10,000 per installation,” Klimaszewski said.
Most access control systems are managed through software that assigns permissions to individual users. That makes it easy to issue new credentials or revoke access immediately when needed.
Tailgating — when an unauthorized person enters behind someone with access — is a common concern. Some
business security systems can flag multiple entries, allowing security teams to respond quickly.
Use modern surveillance to monitor and respond in real time.
Surveillance systems have improved significantly in recent years. Older CCTV setups often produced low-quality footage that was difficult to use, but today’s systems offer much clearer visibility and faster response.
Many businesses now use security cameras that record in HD or 4K, often with signage to make that clear to anyone on-site. With high-speed internet, that footage can be streamed to remote monitoring centers in real time. If something happens, operators can review it right away and decide whether to send a patrol or contact law enforcement.
Klimaszewski recommends choosing cameras with at least 1080p resolution to capture clear, usable footage. “Fuzzy footage can disrupt your security effectiveness, complicating both immediate actions and subsequent analyses,” he said. “High-def cameras are worth the investment for clear-cut evidence and stronger security.”
Another shift is the use of AI to flag unusual activity. Instead of relying on someone to watch multiple screens, these systems highlight potential issues as they happen, allowing operators to respond more quickly and focus on what matters.
Use monitored alarm systems for faster response.
Traditional burglar alarms are easy to ignore, especially in busy areas where false alarms are common. Many businesses now rely on 24/7 monitored alarm systems instead, which alert a security team as soon as an issue is detected.
Klimaszewski says these systems can improve response times and overall security. “When trouble hits, these alarms alert you and the security team, who can respond swiftly, often quicker than the police,” he said.
If a breach is confirmed, security teams or mobile patrols can escalate the situation and contact law enforcement right away, helping reduce delays and limit potential damage.
Secure sensitive documents and records.
Paper documents left out on desks can be easy to remove and may contain information you don’t want leaving your business. Encouraging employees to store documents in locked drawers when they’re not in use — and to collect printouts right away from shared printers — can help reduce that risk.
Digitizing documents can add another layer of protection. Scanning and storing records in a secure cloud-based system makes them easier to manage and control access to. Once documents are uploaded, shredding physical copies can help limit exposure.
Cost-benefit analysis: The financial case for security investment
Understanding the return on your cybersecurity budget is an important part of growth planning. The financial exposure can be significant, and recent data highlights how quickly costs can add up when a breach occurs.
According to IBM’s 2025 Cost of a Data Breach Report, key benchmarks include:
- Average data breach cost: $4.44 million (globally)
- Average cost in the United States: $10.22 million
- Average cost of malicious insider attacks: $4.92 million
- Cost savings with AI and automation: $1.9 million per breach
- Healthcare industry average: $7.42 million per breach
These figures vary by industry and region, but they point to the same conclusion: Security investments can help limit financial exposure and reduce the long-term impact of incidents.
Calculating your security ROI
At a basic level, security ROI comes down to comparing what you spend with what you avoid losing:
(Money saved from prevented incidents − security investment cost) ÷ security investment cost × 100 = ROI percentage
In practice, the calculation is less precise than it looks. You’re estimating the potential cost of downtime, data loss and recovery, then weighing that against what you invest in prevention. For most businesses, the real value shows up in avoided disruption, not just in a percentage.
Insurance and regulatory benefits
Strong security practices can have a direct impact on business insurance costs. Insurers often look at your cybersecurity practices when setting coverage terms, so businesses with stronger protections in place may see lower cyber insurance premiums or more favorable coverage terms.
Security also plays a role in staying compliant with regulations like PCI DSS, GDPR and other industry requirements. Falling out of compliance can lead to fines or limit how you operate, while meeting those standards can make it easier to expand into new markets or work with larger partners.
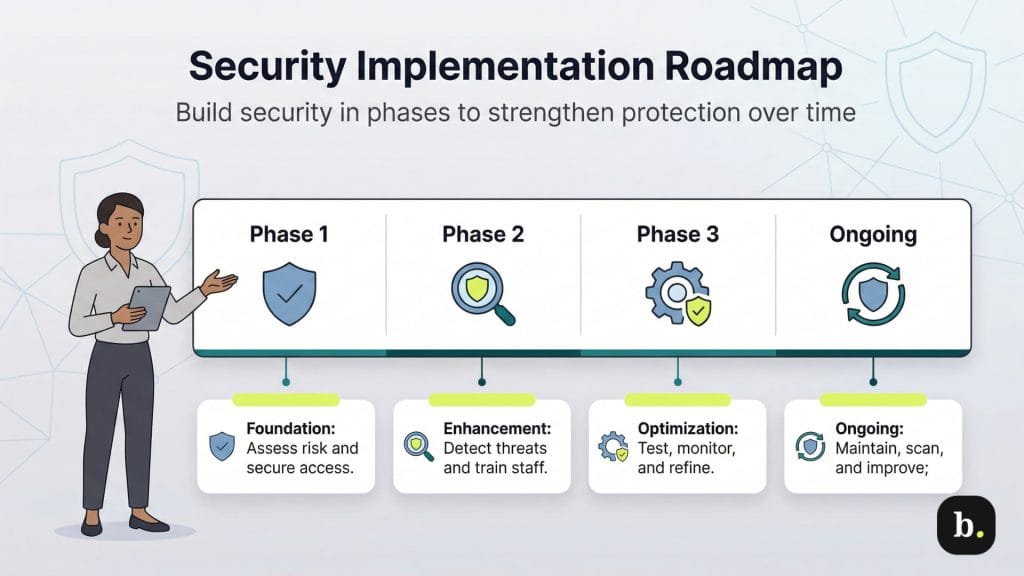
Implementation roadmap: A step-by-step security enhancement plan
Phase 1: Foundation (Months 1-2)
- Start with a cybersecurity risk assessment using the NIST Cybersecurity Framework 2.0 as a baseline.
- Basic access controls should be in place, including multifactor authentication and strong password policies.
- Endpoint protection across all devices is essential.
- Backups should be set up early and tested on a regular basis.
- An incident response plan helps clarify roles and communication if something goes wrong.
Phase 2: Enhancement (Months 3-4)
- Introduce advanced threat detection tools, such as XDR or SIEM solutions.
- Employee training should be rolled out with regular updates.
- It’s also worth reviewing vendor security practices to manage third-party risk.
- Network segmentation can help limit the impact of a potential breach.
- Data loss prevention (DLP) tools can be added where they make sense.
Phase 3: Optimization (Months 5-6)
- Use AI-driven tools to help detect and respond to threats more quickly.
- Run penetration tests and vulnerability assessments.
- Set up continuous monitoring and a simple way to track security metrics.
- Establish a small group or committee to oversee security efforts.
- Revisit and update security policies on a regular basis.
Ongoing maintenance
- Provide regular security awareness training.
- Run periodic vulnerability scans.
- Schedule annual penetration testing.
- Monitor systems continuously and stay current on emerging threats.
- Review security performance and adjust as needed.
Security as a growth catalyst
Your business’s future depends on how well you protect your assets, people and reputation from both internal and external threats. The steps outlined here, from strengthening cybersecurity practices to improving physical safeguards, all play a role in building a more resilient operation.
Security isn’t just another budget line. It affects how reliably your business runs, how customers see you and how confidently you can grow. In a more digital world, trust can be hard to build and easy to lose, and strong security plays a big role in keeping it.