You don’t have to look far to see the repercussions of a business’s failure to protect sensitive information. Equifax, Adobe and Target, among many others, have been victims of significant data breaches that hurt their reputations and bottom lines. Cybersecurity failures can be costly and devastating for businesses of all sizes.
How to protect your business’s sensitive information
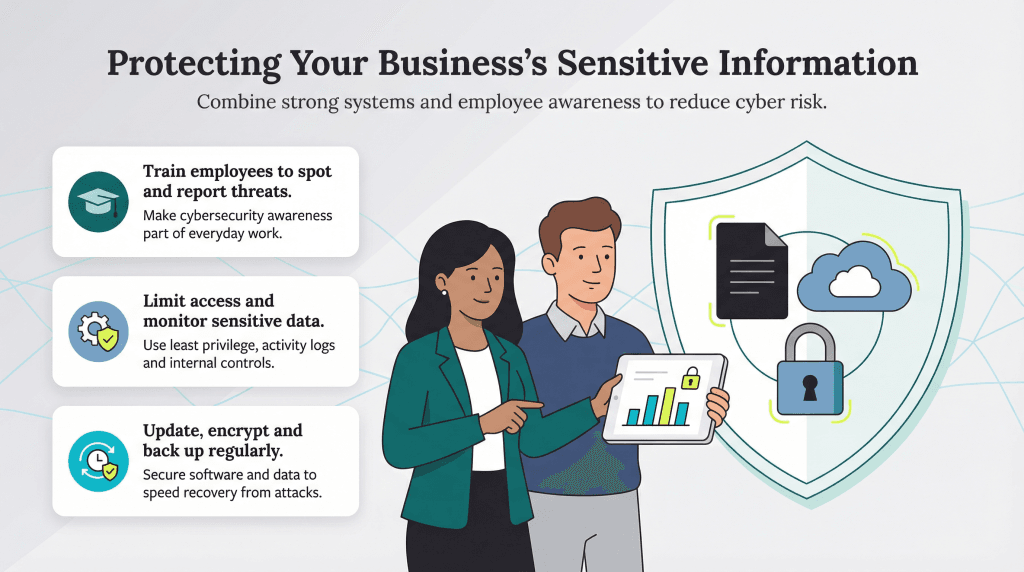
Cybersecurity is a top-down initiative — when leadership prioritizes it, all departments and teams are more likely to follow essential security best practices.
Since every business has unique risks, your first step should be conducting a cyberrisk assessment to identify critical data and assets and determine where your current setup may be leaving them vulnerable. Next, you’ll create a custom cybersecurity plan that includes the infrastructure, policies and procedures needed to mitigate these risks.
However, no matter what your business’s specific cyberrisks, the following 17 best practices will likely be a key part of your strategy.
1. Educate your staff about cybersecurity.
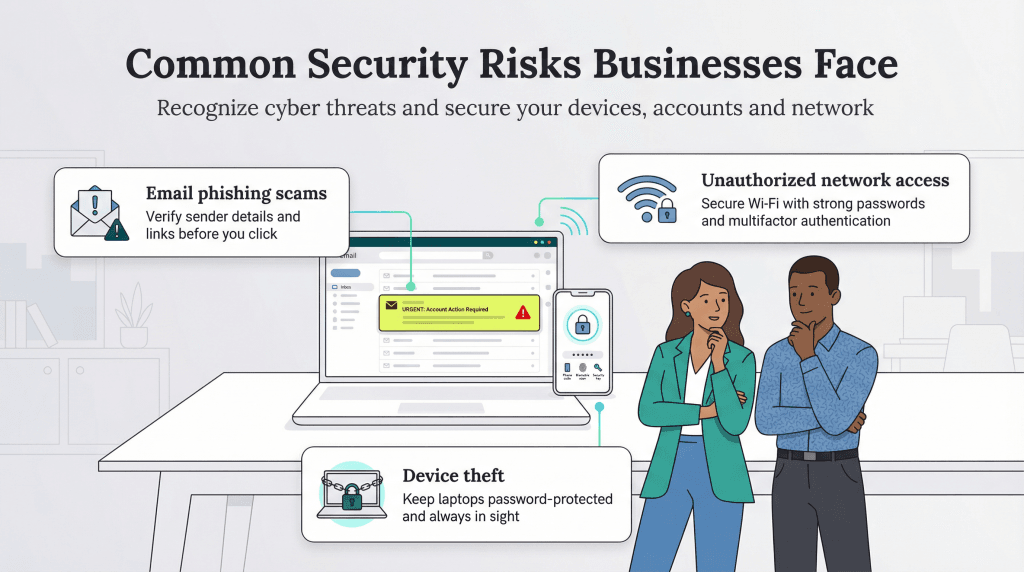
You may have the strongest firewalls and most sophisticated information technology (IT) equipment possible, but none of that matters if your staff unknowingly exposes sensitive data. According to Verizon’s 2024 Data Breach Investigations Report, the “human element” — including honest employee mistakes — accounts for 68 percent of all data breaches.
Your staff may be unaware of hacker tactics, fail to recognize a potential threat or be unsure how to respond in a suspicious situation. For example:
- Would your team know that a request to click a link in an email to reset an account experiencing “unusual activity” is likely an attempt at cyberextortion?
- Would staff members know that an unverified internal call from IT asking for a user’s password could be a social engineering attack?
Employee cybersecurity training is critical. Teach your employees about hackers’ tricks and ensure they know what to look for. Most importantly, provide clear, actionable guidance on what steps to take, including who to notify, if something seems suspicious. Encourage them to report potential threats and show appreciation even if it turns out to be a false alarm.
If you don't have an IT department to spearhead your cybersecurity initiatives, consider hiring a consultant. They'll likely recommend establishing an annual
cybersecurity budget for equipment, software and training.
2. Set internal controls to guard against employee fraud.
Honest mistakes are one thing, but outright employee fraud may also be a concern. Without the right safeguards, rogue employees could misuse company funds, steal customer data or manipulate financial records.
“Employee theft, whether through data breaches or misappropriation of assets, can have devastating financial and operational impacts on a business,” cautioned William Mabotja, an Azure-certified senior software developer at Atlas Finance.
Consider the following best practices to protect your business:
- Limit permissions: Establishing internal controls helps prevent both accidental errors and intentional fraud. “To mitigate the risk of employee theft, businesses should enforce strict internal controls where important tasks, such as editing, creating or deleting resources, should require approval to ensure oversight,” Mabotja advised.
- Restrict employee data access: Mabotja stressed that employee data access should be restricted to only the information they need to do their jobs. “Adhering to the principle of least privilege means that users should only receive the access necessary to perform their required tasks,” Mabotja explained.
- Implement system logs: Ensure your systems log all user activity, tracking which employees access, modify or delete sensitive data.
- Spread out duties: Divide key responsibilities to prevent a single employee from having too much control. For example, instead of having one person approve purchases and review expense reports, assign these tasks to different employees.
- Watch for warning signs: Mabotja advised managers to look for red flags that could indicate fraudulent activity. “Irregular user activity, such as accessing company systems during off-hours, can also signal malicious intent,” Mabotja cautioned.
3. Keep your software updated.
No app or software is 100 percent secure at launch. Loopholes and exploits are often discovered — and cybercriminals will be there to exploit them. While reputable vendors regularly release patches and updates to protect users, it’s up to you to install them promptly.
When creating an SMB cybersecurity plan, ensure that software updates are applied immediately whenever a vendor releases a patch. Delaying updates leaves your systems vulnerable to known threats.
If a vendor stops supporting a product, the security risks increase significantly. In this case, switch to a supported alternative to maintain protection against cyberthreats.
4. Use difficult-to-guess passwords.
For decades, computer security experts have advised both consumers and businesses to create strong passwords for computer networks, online accounts and business applications. This advice is more critical than ever as cybercriminals continue to exploit weak credentials.
To implement safer, systemwide strong passwords, consider instituting centralized password management across your business. In addition, use multifactor, fingerprint or biometric authentication as a second line of defense.
5. Guard your wireless networks.
Don’t be naive about the safety of business Wi-Fi. Although it’s fast and reliable, especially since the release of the 802.11be standard, it’s only as secure as the protocols you put in place.
Here are some tips for protecting your wireless networks:
- Centralize password access for printers, point-of-sale systems and cameras, as they can be a backdoor entryway to your broader network.
- Hide your network from outsiders by turning off service set identifier broadcasting.
- Keep an inventory of permitted devices that can log in to your Wi-Fi; all unauthorized devices will be automatically barred.
6. Use encryption on all types of data.
Encryption transforms data into “ciphertext,” which is indecipherable to anyone without an encryption key. There are three primary types of data:
- In transit (data that’s going from one place to another)
- In use (data that’s being used by a device in a process)
- At rest (data that’s not being used at all)
All three data types are vulnerable to cyberthreats, so it’s best to use encryption across your entire network, including cloud connections. If a breach occurs, hackers won’t be able to make sense of the data.
Sam Neblett, senior augmented reality/virtual reality software developer at international manufacturer Boeing, warned organizations about the risks of unencrypted data leading to intellectual property theft. “Data exposure is a huge concern,” Neblett cautioned. “Unencrypted data, for example, proprietary designs, can be intercepted and stolen, exposing intellectual property and causing businesses to lose competitive advantage.”
Neblett recommends enforcing strong encryption protocols, such as AES-256 for data at rest and transport layer security for data in transit, utilizing secure deployment methods and avoiding the storage of encryption keys or passwords in source code repositories.
Not all data requires encryption. At an organizational level, differentiate between low-risk data that can be stored in plain text and high-risk data that requires encryption — whether on local servers or through
cloud encryption solutions.
7. Back up your data daily.
Regular data backups protect your business from many threats, including hardware failures, accidental deletions, cyberattacks and natural disasters. Without backups, you risk permanent data loss that can disrupt operations and harm your bottom line.
For example, ransomware attacks can lock you out of your computer network and data until a ransom is paid. If your data only exists on your internal network, these attacks can be devastating. Even if you opt to pay the ransom, there’s no guarantee that hackers will release your data — they may still destroy it or leak it online.
However, if you back up your data daily, your IT team or contractor can focus on removing the malware without worrying about losing the only copy of your data. Once the issue is resolved, they can safely restore your software and data back onto your network.
8. Switch to the cloud.
Many companies prefer to store data on physical hardware at their offices, but more businesses are moving to cloud storage services and other cloud solutions — whether entirely or partly. Cloud services go beyond providing storage to offer scalable computing power, automated backups and enhanced security.
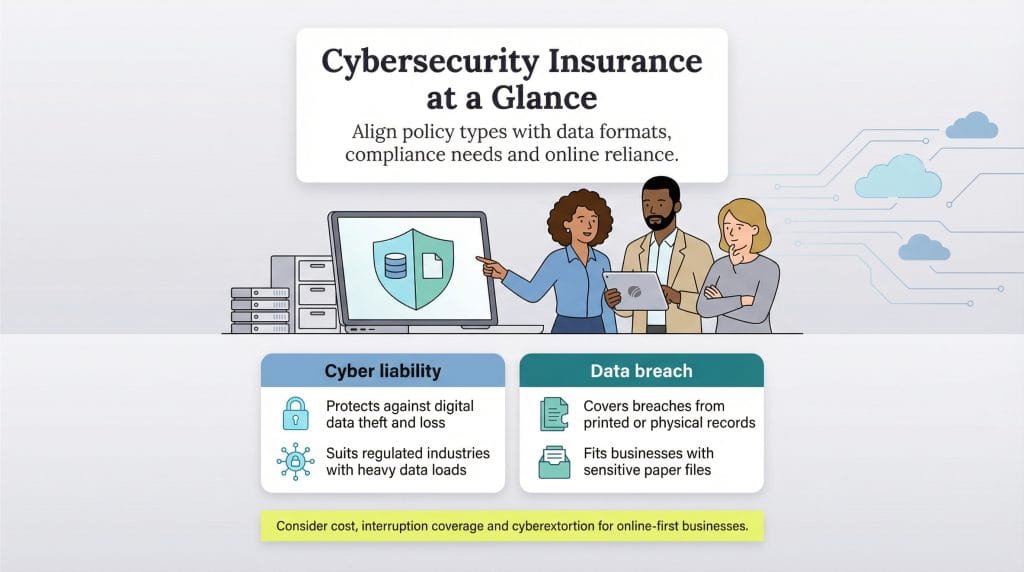
9. Store physical documents securely.
Cyberattacks are a major concern for businesses but lost or stolen physical documents can be just as damaging to business security. Mabotja highlighted the importance of securing sensitive physical documents. “Unauthorized access [to physical documents] often leads to data breaches and the loss of important sensitive information,” Mabotja warned. “If you don’t secure your files…a break-in can result in substantial data losses.”
Keep sensitive documents safe from prying eyes by ensuring secure storage, restricting access and shredding documents that no longer need to be kept. “[Look for] signs of poor physical document security like unlocked file cabinets, easy-to-bypass access controls or little surveillance in areas where you keep sensitive information,” Mabotja recommended.
10. Keep a device inventory.
Consider allowing only authorized devices to log on to your network, cloud and software. That way, team members can securely store and transfer information via laptops, smartphones, tablets and flash drives while ensuring stronger control over device security. If your business has a bring-your-own-device policy, employees can still access necessary resources without compromising security.
However, if a device is lost or stolen or a member of your team who uses it regularly to log in to your system moves to a new employer, you can permanently remove it from your inventory.
11. Save only what’s necessary.
The more customer and company data you collect, the more information you must securely manage and protect. Many businesses store far more data than they need — and if a data breach occurs, their customers may suffer the consequences.
Follow data minimization principles — saving only the information you need to run your business — to limit what hackers could steal. If you only need certain data temporarily, securely delete it as soon as it’s no longer required.
12. Pay expenses with a business credit card.
For business expenses, the most secure payment method is a business credit card. Most business credit cards include zero-liability fraud protection, so if you must dispute a transaction, you won’t lose any money during the investigation process. You can set spending limits on employee cards and receive immediate notifications of transactions via text alerts.
While all payment methods carry some risk, business credit cards offer built-in security features and fraud protections that make them a safer option.
Security isn't the only benefit of
using business credit cards; they also provide detailed expense reports and the opportunity to maximize your travel rewards.
13. Monitor your employees’ accounts.
Any employee account is a potential hacker’s entryway to your business’s sensitive data. To protect your business from employee account hacks, analyze their account activity logs, note their behavior and set up rule-based alerts.
By monitoring login attempts and user behavior, you can identify unusual activity quickly, such as logins from unfamiliar locations or at odd hours — both of which may indicate a compromised account.
14. Create firm employment agreements.
All employment contracts should explicitly prohibit employees from sharing sensitive company information. Every time an employee shares data, they transmit it through a channel that — no matter how secure — could still be vulnerable to breaches. If confidential information isn’t shared unnecessarily, it can’t be compromised.
Additionally, consider incorporating a nondisclosure agreement into your employment contracts. This adds an extra layer of legal protection for your business’s sensitive data — even if technical security measures fail.
15. Plan your response to data breaches.
Disaster preparedness — including security incident response — is crucial in business. How your company reacts to a data breach can mean the difference between a manageable situation and a financial and reputational disaster.
Your response plan should include the following steps:
- Close security gaps immediately. Disconnect and shut down any compromised computers and stop using compromised programs.
- Notify the appropriate parties. Depending on the nature of the breach, you may need to notify customers and law enforcement.
- Investigate the cause. Conduct an internal review or hire a cybersecurity firm to determine what went wrong and how to prevent future incidents.
Mabotja emphasized the importance of managing a business crisis like a breach appropriately to avoid legal consequences. “Acts such as the POPI [Protection of Personal Information] Act in South Africa, the General Data Protection Regulation in Europe and the California Consumer Privacy Act in the United States are part of a global trend towards strict data legislation that [carries] heavy penalties,” Mabotja explained.
A comprehensive incident response plan that follows cybersecurity best practices and regulatory requirements is crucial. “This plan should outline the steps to be taken in the event of a breach, including communication protocols, containment strategies and recovery procedures,” Mabotja added.
16. Stay up to date with your cybersecurity.
Cybersecurity threats are constantly evolving, so outdated systems or software can leave companies — especially smaller ones — vulnerable to cyberattacks.
Mabotja recommends tools like SonarQube to check for signs of outdated cybersecurity measures, such as unsupported software, unpatched vulnerabilities or critical security alerts. “Regularly reviewing system configurations and security logs, alongside these tools, can help organizations identify potential weaknesses,” Mabotja noted.
Mabotja advises taking the following measures to keep your cybersecurity protections current:
- Create a strategy that includes regularly scheduled software updates, security patches and system upgrades.
- Use monitoring tools that alert you to news of vulnerabilities.
- If you have a dev team, schedule time for code reviews and audits to maintain software integrity.
- Use artificial intelligence (AI)-powered tools like Sentinel AI and Microsoft Defender to automate threat detection and response.
United Kingdom-based
financial technology company Finastra, which services many household-name banks, had 400GB of data stolen by a hacker. The breach was discovered after suspicious activity was logged on an internally hosted secure file transfer protocol server.
17. Run regular cybersecurity audits.
Cybersecurity threats are constantly evolving as new attack vectors emerge and are exploited. Conduct a cybersecurity risk assessment at least once a year to validate your previous assumptions about potential threats and vulnerabilities. Evaluate whether your current security measures are effectively mitigating risks.
For newly identified threats, apply the same structured approach:
- Identify what assets are valuable and vulnerable.
- Determine how those assets could be targeted.
- Strengthen defenses using both technological safeguards and employee awareness training.